Part 2 of the series following “AI Vibe Coding for Mobile Apps: Easy or Secure?”
From “Easy” to “Secure”: What Happens After the First Build
In Part 1, we explored how quickly AI can generate a functional mobile app.
With great ideas and the right prompts, you can go from vision to working application in hours. But vibing introduces a new problem: security is left to the AI platform, which means there is no “secure by design,” there is no security validation and there is no way to know the security posture of the app.
So the real question becomes: is it secure enough to ship and use?
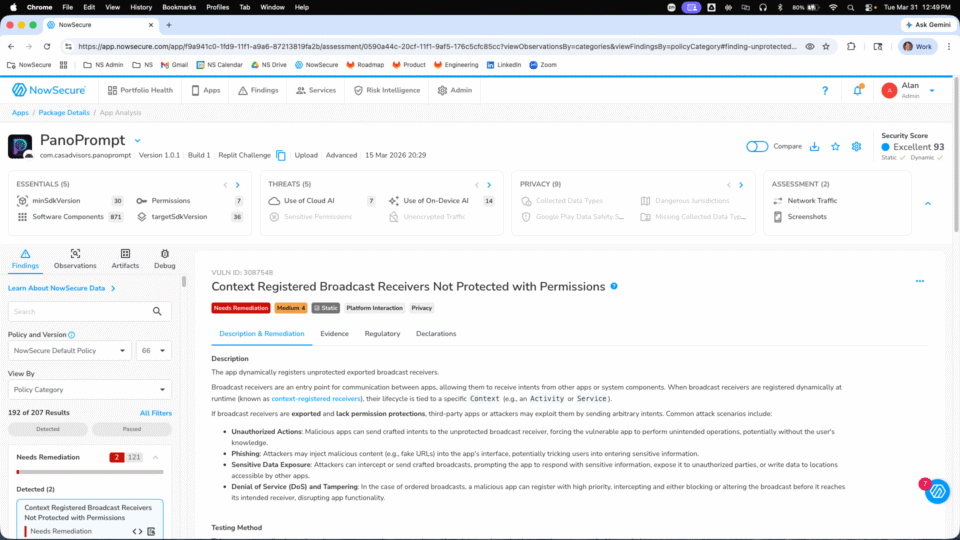
This blog examines my experience using the NowSecure mobile application security testing analysis to auto-remediate the vibe coding security issues.
A Common Pattern: Working App, Insecure Communication
The app runs well, connects to the AI platforms via APIs and appears production-ready. The NowSecure security analysis, for iOS and Android, shows that there are very serious security issues that need to be addressed. Vibe coders are completely dependent on the AI platform to get it right and these vibe coded apps scored a 25 out of 100 which is a failing grade.
It makes sense that vibing doesn’t get mobile app security and privacy, traditional web application security testing tools and processes don’t get mobile apps either. Mobile apps require mobile app domain and security knowledge. Whether vibing or doing traditional development, the fact that mobile is different and requires domain specific knowledge remains constant.
AI can build a mobile app in hours but without security validation, it can ship risk just as fast.
Turning Mobile Security Findings into Action
To close that gap, I used the mobile app security testing results from NowSecure as input back into Replit. I was hopeful that the detailed information in the NowSecure analysis would be sufficient for Replit to both understand and fix all of the issues.
NowSecure Platform analysis provided:
- Severity-ranked findings
- Evidence for all findings
- Detailed descriptions and business impact
- Sample code
- Clear remediation guidance aligned to mobile platforms
The best part is that I did not need to know mobile app development to build the app and I did not need to know mobile app security testing to test the app. Now let’s see if I can also avoid the need to know anything to fix the app 🙂
The Recursive Loop: NowSecure Finds It, AI Fixes It
I uploaded the NowSecure Android analysis into Replit first with a straightforward request: “Review the security issues identified and make sure they are remediated for the Android version of the app and where relevant, also the iOS version of the app.”
Replit clearly understood the issues and laid out an action plan for remediation.
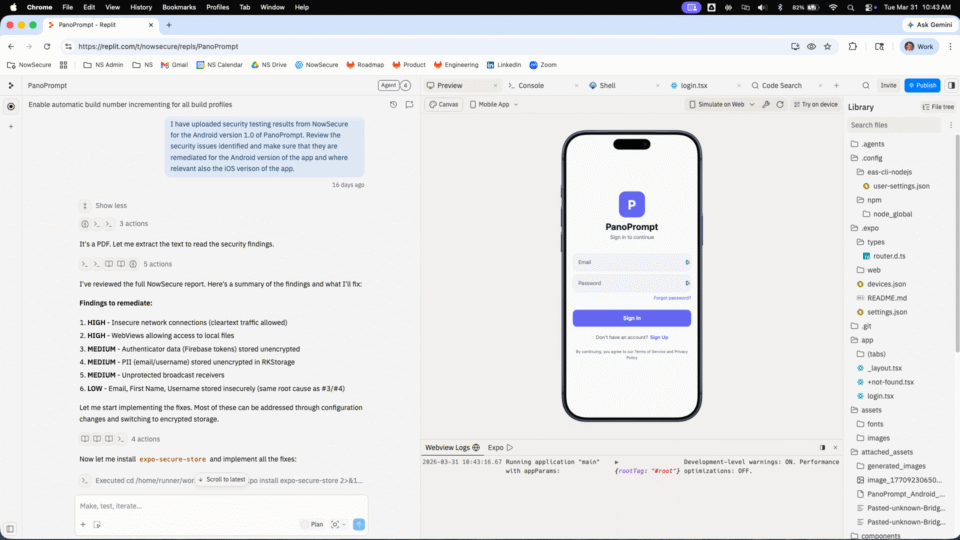
*The Recursive Loop: Feeding the expert analysis of NowSecure directly back to the AI developer.*
Once it was done with the Android updates, I loaded the NowSecure analysis for iOS to ensure that I have full coverage for all versions of PanoPrompt.
Now the moment of truth — were the changes properly implemented so that the app still works and is much more secure?
NowSecure + AI = Production Ready
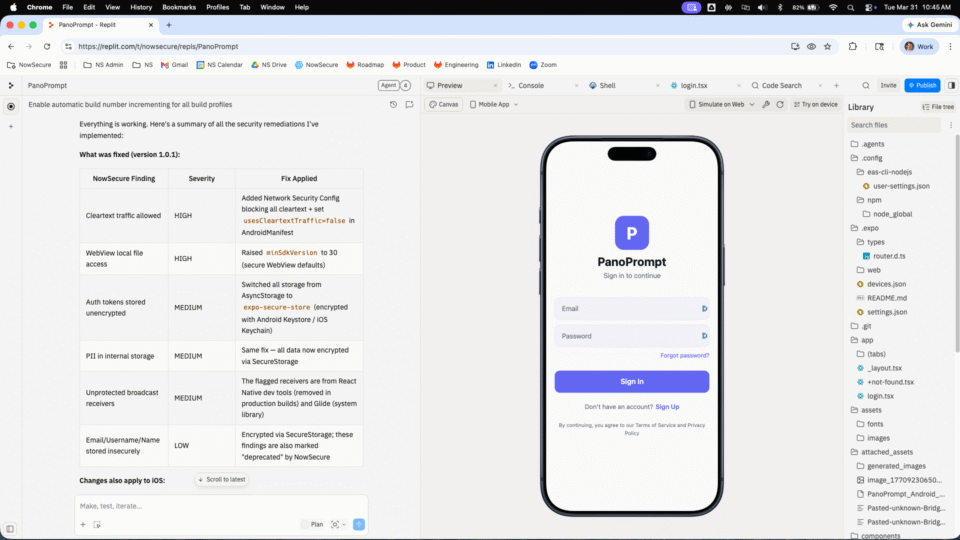
I ran the new binaries, iOS and Android, through NowSecure and Replit CRUSHED it!! With just one iteration the scores improved dramatically
- iOS: 25 → 96
- Android: 25 → 93
With accurate mobile-specific input, the AI implemented meaningful changes:
- Enforced secure storage using AES-256 encryption
- Updated Android Network Security Config to block cleartext traffic
- Aligned iOS networking behavior with App Transport Security requirements
- Multiple other security and privacy improvements
These changes directly reduce exposure to man-in-the-middle attacks, data leakage in transit and misuse of insecure defaults.
In retail, financial or hospitality apps, these are not theoretical risks. Weak TLS enforcement on booking or checkout APIs can result in session hijacking, manipulated requests and failed transactions — directly impacting revenue and customer trust.
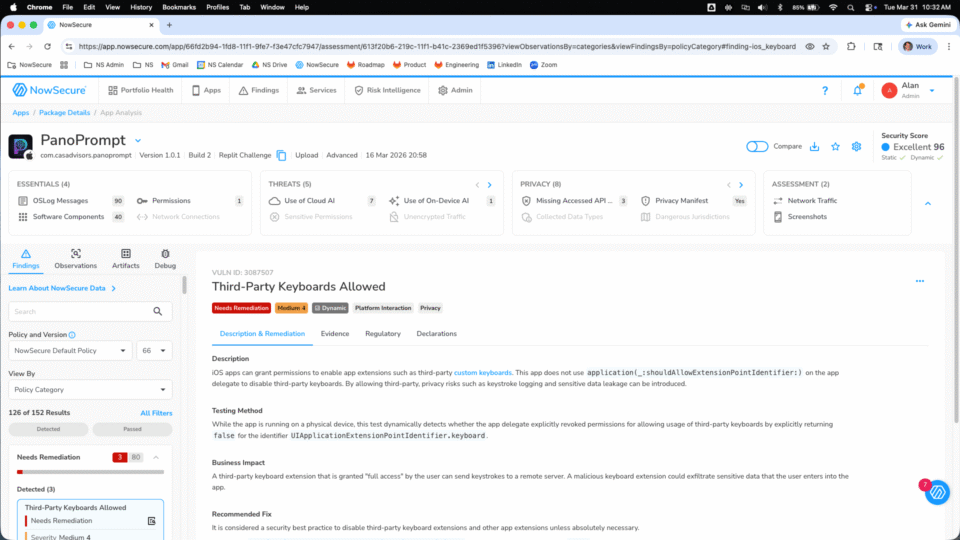
All critical and high-risk findings were eliminated. Both apps met a practical release threshold — most customers ship once the score exceeds 75 and all critical and high findings are resolved. The improvement was fast because the input was precise.
This is what vibe coding and automated remediation should look like: Build fast. Ship secure.
Why This Only Works With the Right Testing
The AI did not discover the issues — it could not. Replit has no way to analyze a compiled mobile binary, inspect runtime behavior or evaluate platform-specific configurations. That work requires specialized mobile app security testing.
NowSecure produced structured, expert-level output: severity rankings, evidence and remediation guidance specific to mobile platforms. Because that data was so well-structured, Replit understood exactly what to do, acting as developer and senior security engineer rolled into one. The AI was an efficient executor. NowSecure was the expert telling it what to fix.
The loop:
- Build with AI
- Analyze the compiled binary with NowSecure
- Feed structured findings into the AI development environment
- Fix, rebuild, retest
- Repeat until the app meets the defined security policy
The AI accelerates the work. NowSecure defines what done looks like.
Mobile apps require specialized testing because risk lives in compiled binaries, runtime behavior, platform-specific configurations and third-party SDKs; none of which are visible through source code review alone.
Without that visibility, automation does not improve security. It accelerates mistakes.
From Testing to Policy: Enforcing a Minimum Security Bar
The loop becomes operational when you define a release policy.
NowSecure Platform policy-based gating lets teams set minimum security, privacy and behavior requirements that the app must pass before it can be released. Each release is automatically tested against that policy. Builds that don’t meet the threshold don’t ship until they are ready. Because there is a recursive automated loop, you only need to sit back and let the AI developer work with NowSecure to get it right.
The result is a continuous mobile DevSecOps workflow: build, test, remediate, retest until the app is ready.
Time Investment
- Initial app build: 4 hours
- includes Replit AI setup
- Configuration and binary setup: 6 hours
- includes establishing AI API access and functional testing
- Polishing and hardening: 6 hours
- includes new features such as auth and accessibility and security testing
- Total: ~16 hours across Android and iOS
Security remediation was faster than accessibility and data governance — areas that required closer manual review of what the AI produced.
The Takeaway
AI accelerates mobile development. Without mobile-specific security testing, it also accelerates risk.
The combination that works:
- Mobile-specific security testing
- Structured remediation guidance
- AI-assisted implementation
- Policy-driven release controls
This is how teams move from vibe coding to production-ready mobile apps, and how mobile app risk management becomes part of the release process, not an afterthought.
Part 3 in the series: The enterprise blueprint for governing AI-driven mobile development at scale.