How enterprise mobility teams can detect hidden AI features and reduce mobile app risk.
Enterprise mobility and security teams face a growing challenge: AI capabilities quietly appear inside the mobile apps employees use every day, creating mobile shadow AI risk.
TL;DR
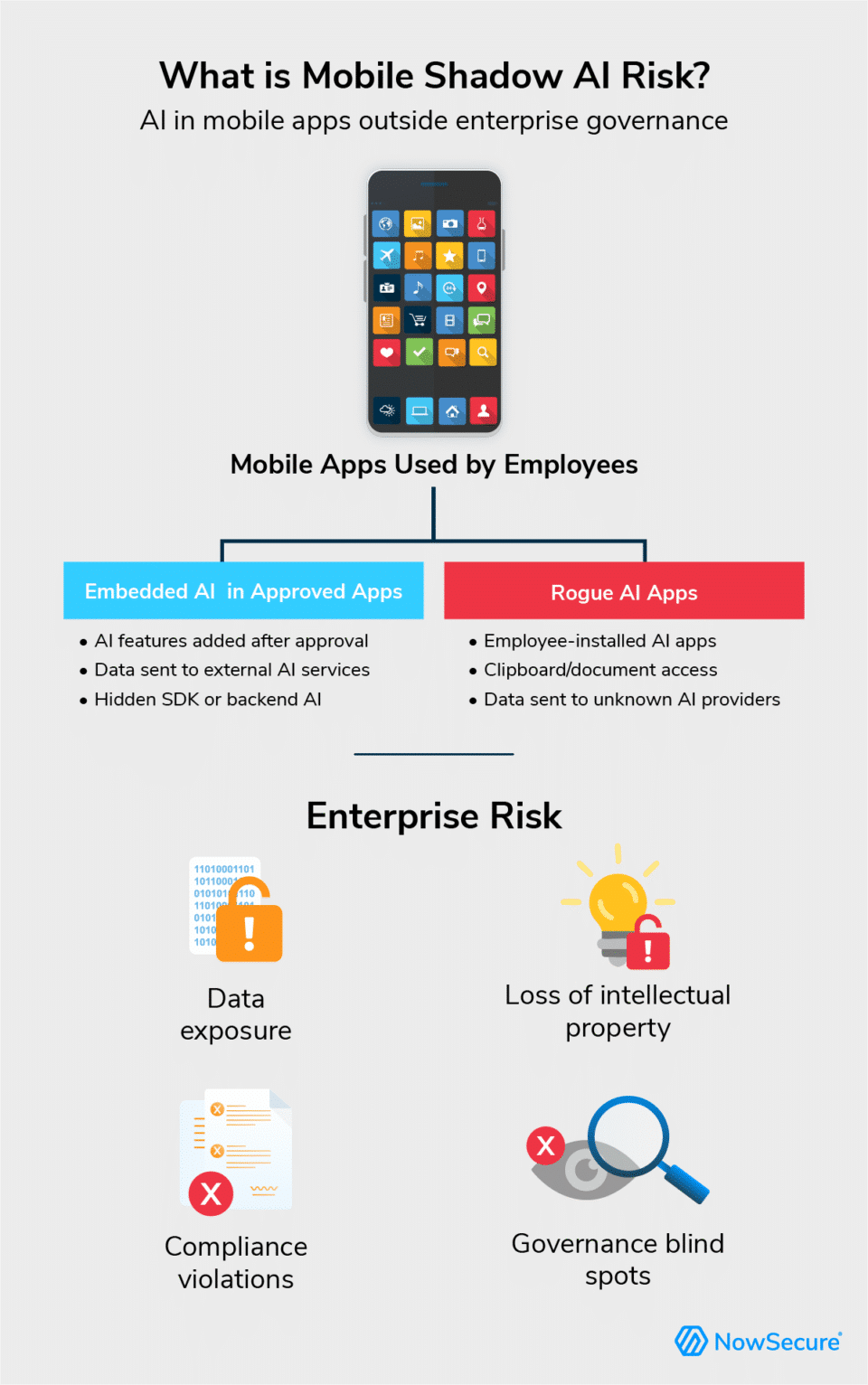
- Mobile shadow AI risk occurs when AI capabilities operate inside approved third-party mobile apps or rogue AI apps outside enterprise governance controls.
- Embedded AI features in mobile apps can process sensitive data or connect to external AI services, creating enterprise mobility, data security and compliance risk that traditional mobile app vetting often misses.
- Continuous visibility into third‑party mobile app behavior strengthens AI governance, while solutions like NowSecure Mobile App Risk Intelligence (MARI) enable mobility teams to detect hidden risks across their app portfolios.
Enterprise mobility teams approve hundreds — sometimes thousands — of third‑party mobile apps for employee use. Many now include AI features that operate quietly in the background, analyzing user data, sending information to external AI services and introducing new data flows that rarely appear in governance reviews.
These hidden capabilities create mobile shadow AI risk — AI functionality running inside approved apps or accessed through AI-powered apps outside enterprise oversight. As organizations tighten AI policies, these features can bypass AI governance controls, expand enterprise mobility risk and expose sensitive data.
Mobile shadow AI risk represents an emerging governance challenge for enterprise mobility teams.
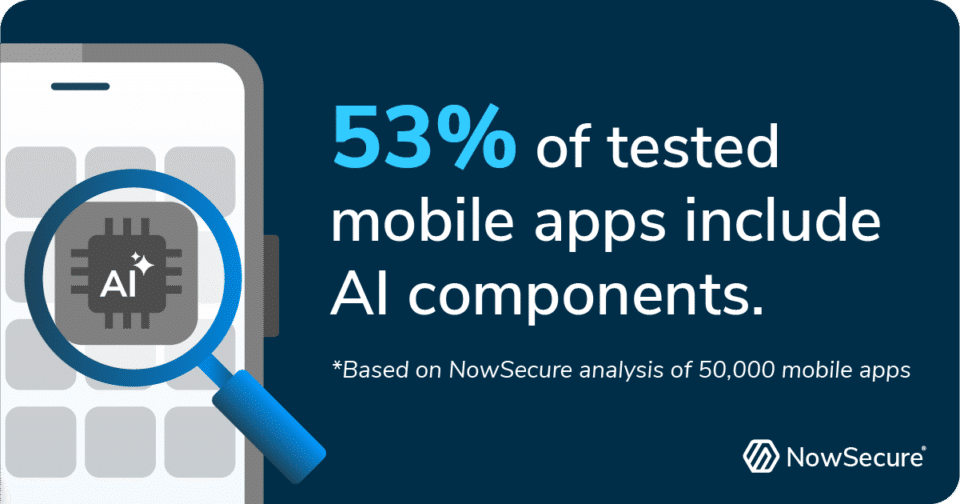
NowSecure research shows that out of 50,000 mobile apps tested during February alone, over 53% included AI components. That number continues to rise as developers rapidly embed AI features into mobile apps. For enterprise mobility managers and end-user computing (EUC) leaders, traditional app approval processes no longer provide enough visibility to manage this risk.
Security leaders increasingly recognize that hidden AI capabilities create real enterprise risk. Gartner® warns that “the rapid adoption of unsanctioned AI tools can lead to both visible and invisible impacts such as IP loss, data exposure and increased security risks” The firm “predicts that by 2030, more than 40% of enterprises will experience security or compliance incidents linked to unauthorized shadow AI.”
“To address these risks, CIOs should define clear enterprise-wide policies for AI tool usage, conduct regular audits for shadow AI activity and incorporate GenAI risk evaluation into their SaaS assessment processes,” said Gartner Distinguished VP Analyst Arun Chandrasekaran in a recent press release.
While this guidance typically focuses on SaaS platforms and employee AI tools, the same governance challenge extends to mobile apps where embedded AI features or rogue AI apps can operate outside traditional oversight and introduce new third-party mobile app risk.
What Is Mobile Shadow AI Risk in Mobile Apps?
Mobile shadow AI risk refers to AI functionality embedded in or accessed through mobile apps operating outside enterprise governance controls. Mobile shadow AI often appears in apps that have never undergone rigorous mobile application security testing.
For example, a productivity app approved for enterprise use adds a new AI assistant feature through a routine update. When employees use the feature to summarize meeting notes or analyze documents, the app sends content to an external AI service for processing outside formal governance review.
Mobile shadow AI risk typically appears in two ways:
AI Embedded in Approved Third-Party Apps
Many popular productivity, CRM, collaboration, HR, fintech and analytics apps now integrate AI-powered capabilities. These features may:
- Analyze user input using external AI services
- Process customer or employee data in cloud-based AI systems
- Transmit data to backend systems in high-risk jurisdictions
- Introduce new data flows through silent feature updates
An app approved last quarter may add AI-driven features today – a growing concern as organizations adopt AI-enabled software without comprehensive mobile app security assessments. That evolution increases third-party mobile app risk without triggering a new AI governance review. To learn more about governance controls for AI-powered apps, see NowSecure’s guide to AI governance for mobile apps.
Rogue AI Apps Installed on Corporate or BYOD Devices
Employees may also download standalone AI apps onto corporate-managed smartphones, tablets or BYOD devices connected to enterprise systems.
These applications can:
- Access clipboard data
- Capture screenshots or documents
- Analyze email or messaging content
- Transmit business information to external AI providers
If your organization restricts which AI services workers may use, this behavior directly undermines AI governance policies. Even with mobile device management controls in place, shadow AI apps can slip into the environment and introduce unintended data exposure.
Why Does Mobile Shadow AI Create Enterprise Mobility Risk?
Enterprise mobility leaders sit at the intersection of productivity, compliance and security. When AI operates invisibly inside mobile apps, they introduce several enterprise risks.
How AI Creates Data Security Risks
Mobile apps frequently access sensitive information, including contacts, location data, internal documents, customer records and corporate communications. When AI services process that data externally, organizations may lose control over how it is handled, retained or shared and violate privacy.
If backend AI systems reside in dangerous jurisdictions or operate under unclear data handling practices, exposure increases significantly.
How AI Creates Mobile App Compliance Risk
The rise of global and state-level AI regulations has pushed organizations to strengthen AI governance. These rules place new obligations on companies that develop, deploy and use AI systems, particularly when those systems process sensitive data. Regulations such as the EU AI Act and emerging U.S. state laws increasingly require transparency, accountability and stronger controls over automated decision-making.
As a result, many enterprises now enforce formal AI governance frameworks that include:
- Approved AI vendor lists
- Data residency requirements
- Cross-border data transfer restrictions
- Documented AI usage policies
Approving an app that embeds AI functionality — or allowing rogue AI apps on managed devices — can quietly violate these policies. That creates audit exposure and weakens defensibility during compliance reviews.
When employees use unapproved AI services, the enterprise loses visibility into data flows and the ability to demonstrate compliance. This lack of control increases exposure to regulatory fines, data leakage and intellectual property loss and makes it difficult to explain AI-influenced decisions during audits or investigations.
Enterprise mobility risk grows when governance policies lack technical validation.
How Shadow AI Appears in Mobile Apps
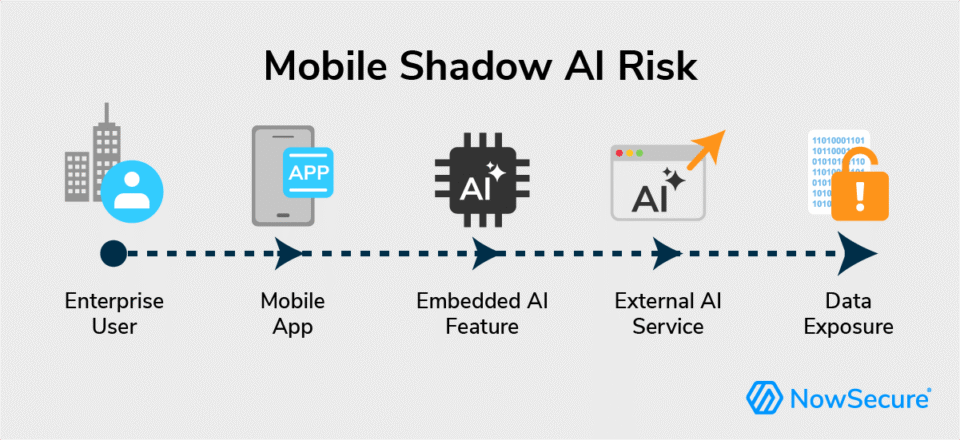
Shadow AI rarely appears as a standalone AI app. Instead, AI functionality often operates behind the scenes inside mobile apps.
AI capabilities often appear through embedded SDKs, machine learning frameworks or API calls to external AI services. For example, apps may integrate AI SDKs for recommendation engines, connect to generative AI APIs for text processing or rely on backend inference services for analytics. Mobility and security teams can often detect these integrations by identifying AI-related network endpoints, AI service domains, SDK libraries or unusual data transmission patterns during runtime analysis.
Examples include:
- AI-driven recommendation engines
- AI-powered chat or support features
- Document or image recognition tools
- Behavioral analytics and personalization
- Generative AI assistants embedded in apps
These capabilities may operate through backend AI services or server-side processing, making them difficult to detect during traditional mobile app vetting.
Why Traditional App Approval Processes Miss Mobile Shadow AI
Most enterprise mobility workflows focus on:
- App store reputation
- Permission analysis
- Vendor questionnaires
- Privacy disclosures
But those steps rarely uncover embedded AI components, backend AI endpoints, runtime network behavior or silent feature rollouts introduced through updates.
As AI adoption grows, third-party mobile app risk evolves quickly. App behavior can change without a new approval request. Governance frameworks that rely on one-time app reviews cannot keep pace with rapidly evolving AI capabilities.
What Should Enterprise Mobility Teams Do About Mobile Shadow AI?
To manage mobile shadow AI risk effectively, enterprise mobility teams must move beyond policy enforcement and into continuous visibility.
Enterprise mobility teams can reduce mobile shadow AI risk by adopting a structured process to identify AI features, monitor app behavior and continuously evaluate third-party mobile apps.
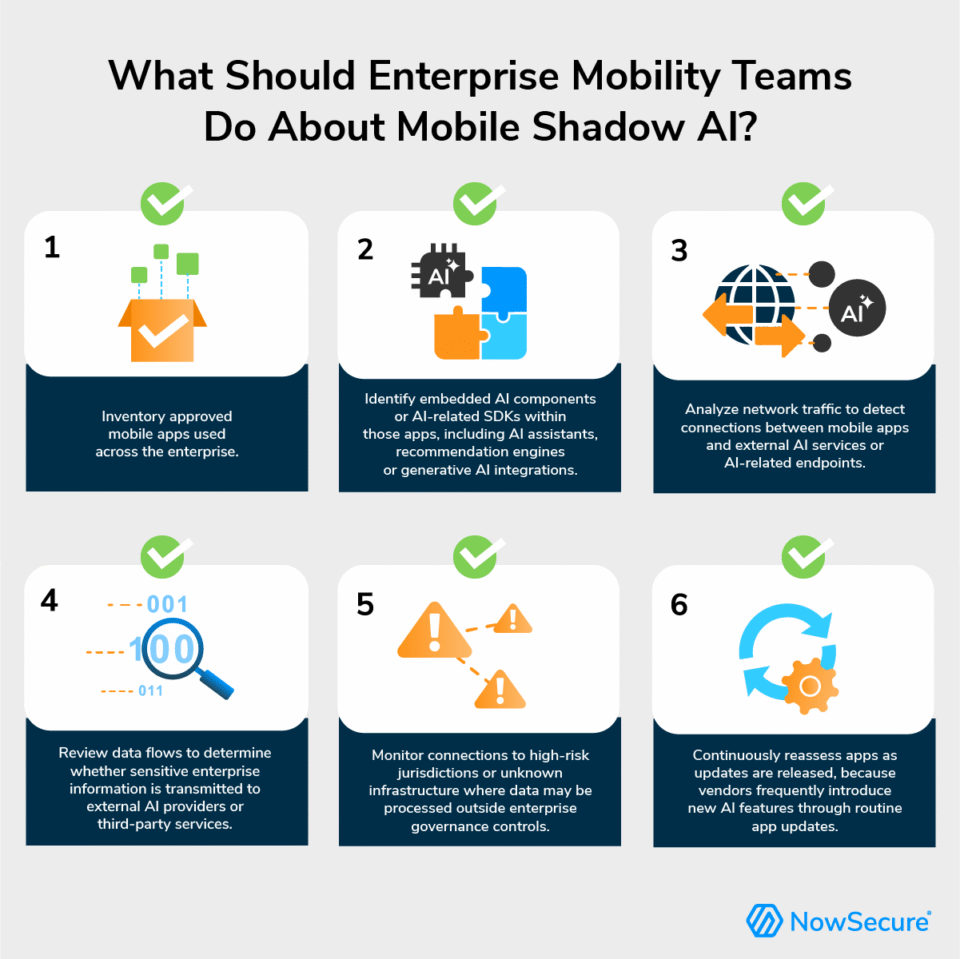
Operational checklist:
- Inventory approved mobile apps used across the enterprise.
- Identify embedded AI components or AI-related SDKs within those apps, including AI assistants, recommendation engines or generative AI integrations.
- Analyze network traffic to detect connections between mobile apps and external AI services or AI-related endpoints.
- Review data flows to determine whether sensitive enterprise information is transmitted to external AI providers or third-party services.
- Monitor connections to high-risk jurisdictions or unknown infrastructure where data may be processed outside enterprise governance controls.
- Continuously reassess apps as updates are released, because vendors frequently introduce new AI features through routine app updates.
This approach strengthens AI governance in mobile apps, improves EUC security posture and supports defensible approval decisions backed by objective evidence.
Organizations managing third‑party mobile app risk can also explore NowSecure’s third‑party mobile app risk ebook or download the mobile app risk management (MARM) ebook for practical guidance on evaluating and governing enterprise mobile apps.
Detecting these risks requires more than policy enforcement — it requires continuous visibility into how mobile apps behave.
How NowSecure MARI Reduces Mobile Shadow AI Risk
NowSecure Mobile Application Risk Intelligence (MARI) enables enterprise mobility and EUC teams to assess and monitor third-party mobile app risk at scale. Teams can also explore insights from the free NowSecure Mobile App Risk Checker (MARC) for insight into mobile app risk indicators and behaviors across widely used apps.
With MARI, organizations can:
- Evaluate millions of public mobile apps
- Surface risky behaviors and embedded components
- Monitor app changes over time
- Identify indicators relevant to AI data security risk
- Support enterprise mobility risk decisions with clear evidence
You can explore additional resources in the NowSecure knowledge center or schedule a demo to see how MARI helps detect shadow AI in mobile apps and reduce Mobile Shadow AI Risk across your approved app portfolio.
The Bottom Line: Mobile Shadow AI Risk Requires Active Governance
Mobile shadow AI risk introduces a new governance challenge for enterprise mobility teams. AI capabilities embedded in approved apps — or installed through rogue AI applications — can expand enterprise mobility risk, increase data security exposure and create mobile app compliance issues without clear visibility.
Organizations that proactively govern AI in their mobile environments will strengthen AI governance, reduce third-party mobile app risk and make confident, defensible decisions.
Gartner Press Release, Gartner Identifies Critical GenAI Blind Spots That CIOs Must Urgently Address, November 19, 2025
GARTNER is a trademark of Gartner, Inc. and/or its affiliates.
FAQ: Mobile Shadow AI Risk
What is mobile shadow AI?
Mobile shadow AI describes AI functionality running within mobile apps on enterprise or BYOD devices outside formal governance or policy controls. Examples include AI embedded in approved apps or rogue AI apps installed by employees.
Why is shadow AI in mobile apps a data security concern?
AI features embedded in mobile apps can process sensitive data, connect to external AI services or transmit information to unknown jurisdictions. Without visibility, these behaviors can create data security, compliance and enterprise mobility risks.
How can organizations detect shadow AI in mobile apps?
Effective detection requires continuous mobile app risk monitoring that identifies embedded components, analyzes network behavior and tracks app updates that introduce new functionality.
How does NowSecure MARI help manage mobile shadow AI risk?
NowSecure MARI provides risk intelligence on millions of public mobile apps, helping enterprise mobility teams evaluate third‑party apps, identify hidden risks and make informed approval decisions.