On Oct. 25, 2022, OpenSSL began pre-notifying organizations of two critical vulnerabilities in OpenSSL 3.0.x. On the positive side, OpenSSL 3.0 had not been widely deployed yet, and even better on Nov 1, 2022, the two vulnerabilities were downgraded from critical to high. However, on the heels of other recent highly impactful vulnerabilities like Log4j and the devastating widespread impacts of the earlier OpenSSL “Heartbleed” vulnerability from 2014, defenders went on high alert… and so did we.
We found 1,529 instances of OpenSSL across 608 apps.
Popular Mobile Apps with OpenSSL
We analyzed 3,845 very popular mobile apps from our MobileRiskTracker™ to see if any mobile app contained a direct or transient OpenSSL dependency and if so, if that version was vulnerable. Overall, Android apps represent roughly 90% of popular mobile apps with OpenSSL and iOS at 10%.
The good news is that we didn’t find mobile apps exposed to the recent OpenSSL 3.0.x vulnerabilities just announced. But there are substantial issues with mobile apps using older versions of OpenSSL that have known vulnerabilities. Specifically we found 1,529 instances of OpenSSL across 608 apps (~16%) with the following issues:
- 98% of OpenSSL versions in these popular mobile apps have publicly disclosed vulnerabilities
- 86% of the vulnerable versions have a severity of HIGH
- 30% are of OpenSSL versions in popular mobile apps are fully unsupported
- 57% are either unsupported or require premium support (OpenSSL 1.0.2 branch)
Digging into these mobile apps using our Software Bill of Materials (SBOM) mobile analysis, we found that OpenSSL is most often included via third-party SDKs (identified as transient dependencies). Note SQLCipher is the most common dependency that includes the OpenSSL library. I enumerate a lot more detail on the top libraries and dependencies in my personal VLOG on SBOMs here.
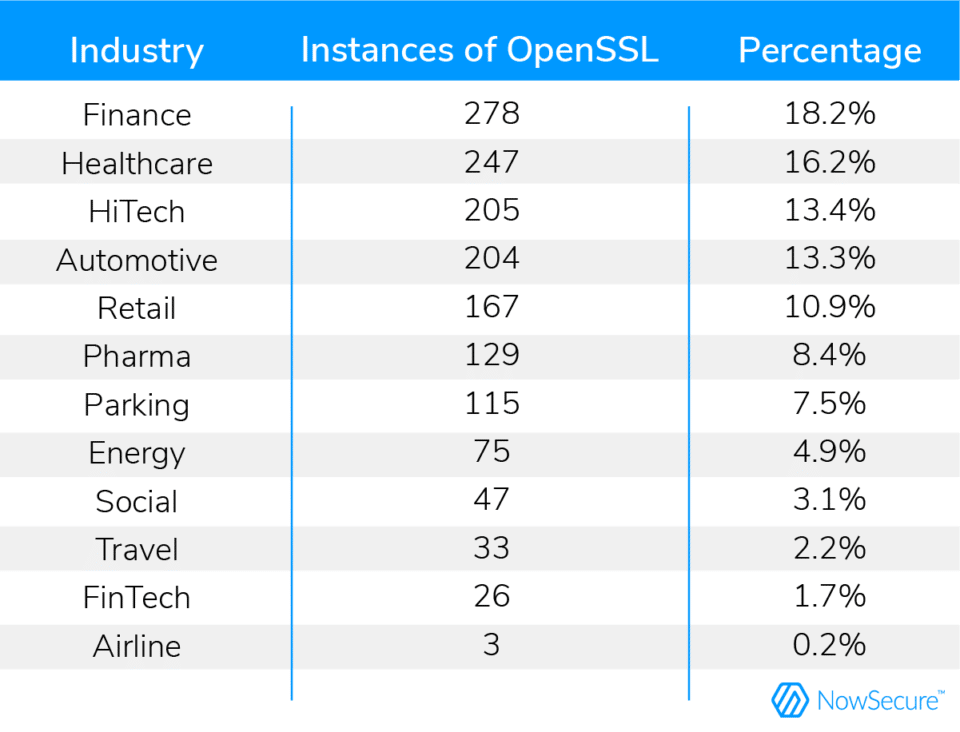
It’s also interesting to look at the impacted mobile apps by industry vertical:
How to Detect OpenSSL In Your Mobile App
There are two primary categories of mobile apps you should consider checking:
- Apps you build
- Apps you use
Our NowSecure Platform provides automated analysis of the mobile apps you build and use, using binary analysis to identify vulnerabilities and dynamically generate SBOMs as well.
To learn more about SBOMs, jump over to my recent tutorials I’ve been sharing here. For a deeper dive into how I ran the analysis above and to learn how to perform your own OpenSSL mobile app analysis, please jump over to my VLOG and watch How to detect OpenSSL v3.0 and Heartbleed vulnerabilities in mobile apps.