The March 2026 axios npm supply-chain attack compromised developer machines, exposed CI/CD pipeline secrets and — in apps using OTA update mechanisms like CodePush — gave attackers a path to production without touching App Store review.
A software supply-chain attack targets the dependencies, build systems and distribution pipelines used to create applications — rather than the application code itself.
On March 30, 2026, one of the most widely used JavaScript libraries, axios, was compromised. Downloaded over 100 million times weekly, axios was weaponized by an attacker to deploy a Remote Access Trojan (RAT). As a result, this malicious payload was delivered directly into the development environments of companies globally.
If your organization ships a mobile application built on React Native, Ionic or any JavaScript-based framework, this is a direct risk to your development and build environments — and a downstream risk to every mobile app you ship.
What Was the Axios NPM Supply-Chain Attack?
The March 2026 axios npm supply-chain attack exposed a critical gap in mobile app security — impacting developer machines, CI/CD pipelines and potentially the apps shipped to users.
A Trusted Name, A Hidden Threat
The attack was elegant in its simplicity. The attacker did not rewrite axios. They did not introduce malicious code that a scanner could flag. Instead, they compromised the account of axios’s primary maintainer, published two poisoned versions of the package (1.14.1 and 0.30.4), and added a single line to a configuration file that pulled in a hidden malicious dependency.
The dependency’s sole purpose was to secretly install a Remote Access Trojan (RAT), giving an attacker persistent remote control of the compromised machine.
To make detection even harder, the malicious code deleted itself after execution, replaced the evidence with a clean file and swallowed all error messages so that the installation appeared to complete successfully. Any developer who ran a routine dependency update that day had no warning, no error and no indication that anything had gone wrong.
The correct question is not whether the dropper reached users — it’s what an attacker can do with the access they gained.
Why the Axios NPM Supply-Chain Attack Creates Unique Mobile App Security Risks
Mobile applications carry a category of risk that traditional application security programs don’t address.
A web app can be patched in minutes. A compromised mobile binary must clear App Store or Google Play review, then rely on user adoption. Mobile builds bundle their entire dependency tree — including a poisoned axios — directly into a signed binary.
And in applications that use Over-The-Air update mechanisms like CodePush or Expo Updates, an attacker who controls your build pipeline can push malicious JavaScript bundle updates to already-installed apps, bypassing app store review entirely.
This fundamentally changes the blast radius of a supply-chain attack.
For organizations building mobile apps with frameworks like React Native or Ionic, these dependencies are integrated into the build process, meaning a compromise in development or CI/CD environments can directly affect what gets shipped to users. This highlights a common gap in enterprise security strategies: insufficient visibility into the integrity of third-party components and the environments where mobile applications are built.
When mobile apps are built with JavaScript frameworks, their dependencies, like a compromised version of axios, are bundled directly into the application binary. This means the compromise can affect the environment where the application is built, which in turn can impact what gets packaged and distributed to customers via the App Store and Google Play. Consequently, users may be at risk if an attacker leverages that compromised environment to modify what gets built or distributed.
The risk compounds across three critical areas:
- Developer machines: Engineers who executed
npm installduring the compromise window might have inadvertently exposed sensitive local environment data. This includes app signing certificates, provisioning profiles, API keys, and credentials that grant access to cloud infrastructure and production systems. - Build pipelines: Your CI/CD pipeline is where mobile apps are assembled and signed before release. These environments typically hold some of your most sensitive secrets: App Store and Play Store publishing credentials, push notification keys, and cloud access tokens. An attacker with access to those pipelines can do far more damage than simply stealing source code.
- Shipped applications: A mobile release compiled while the malicious
axiosversion was active could have been built in a compromised environment, potentially resulting in a tampered production build. Any tampered build produced from a compromised environment could persist on user devices until a clean version is released and adopted.
Unlike a web application where a patch can be deployed in minutes, a compromised mobile release requires app store submission, review and user adoption of the update. That cycle takes days. During that time, the exposure is entirely outside your control.
A compromised mobile build pipeline doesn’t hit every organization equally. But in every case, the consequences are high:
- Financial services: Exposure of session tokens, payment authentication flows and credentials used to sign transactions.
- Healthcare: Risk to PHI and potential HIPAA breach notification triggered by compromised build environments
- Government and defense: Reportable incidents under FedRAMP or DISA STIG due to pipeline integrity loss
- Retail and travel: Revenue impact, fraud, payment compromise and customer trust erosion from forced app updates or pulled releases
Can I Trust That Mobile App?
One of the most common questions executives ask when a supply-chain attack like this surfaces is: “Are our users — the people who downloaded our app from the App Store or Google Play — and our Intellectual Property, actually at risk?”
The answer requires an important distinction.
The RAT delivered by the axios attack ran during software installation on developer machines and build pipelines. It did not execute on an end user’s phone when they opened your app. In that narrow sense, customers who downloaded your app from the App Store were not directly exposed to the dropper itself.
But that is not where the story ends.
The true danger to users emerges after a development environment is compromised, dwarfing the initial threat of the dropper. If an attacker leverages a developer machine infected with the axios Remote Access Trojan (RAT) to gain access to your build pipeline, they essentially gain control of your mobile deployment infrastructure. This critical access allows them to submit a malicious app update to the App Store using your company’s identity. Even more concerning, they can push silent, malicious JavaScript bundle updates — in applications that use Over-The-Air (OTA) mechanisms such as CodePush or Expo Updates — to already installed instances of your application.
In apps that support OTA updates, this mechanism can bypass App Store and Google Play reviews and reach users directly, at the next time they open it, with no warning.
App store review processes are not designed to detect compromises originating in build pipelines or post-release update channels. They can verify that a binary matches a known malware signature, but they cannot perform the behavioral analysis required to detect a novel, supply chain-staged payload that was clean at review time and malicious at runtime.
This is why the scope of a supply-chain incident cannot be evaluated by asking whether the initial dropper reached users. The correct question is not whether the dropper reached users — it’s what an attacker can do with the access they gained. In the axios case, that access included the potential to reach every user of every mobile app built on the affected pipeline, without ever touching the App Store review process at all.
What Should You Do if Your App Uses a Compromised Axios Version?
Treat your build environment as compromised.
- Rotate every secret your CI/CD pipeline could reach, including App Store credentials, signing certificates and PI keys.
- Identify all builds produced during the exposure window.
- Determine whether a forced app update or store removal is required.
- Don’t rely on a clean node_modules folder as evidence — the malicious code deletes itself after execution.
Why Traditional AppSec Tools Miss Supply-Chain Attacks Like Axios
The axios attack was specifically designed to defeat the security tools most organizations rely on.
Conventional Software Composition Analysis (SCA) tools are designed to identify known vulnerabilities by cross-referencing dependencies against established databases. However, this attack bypassed such defenses entirely, utilizing a newly created package. Because the package was brand-new, it lacked a CVE record, prior history and any existing flags, meaning traditional SCA tools were unlikely to recognize it as a threat.
Static code analysis tools inspect source code for suspicious patterns. axios’s primary source code did not contain obvious malicious logic. The entire attack lived in a single configuration file.
And because the malicious code deleted itself after running, even a post-incident forensic review of the node_modules folder would show nothing out of the ordinary.
This is the new reality of software supply-chain attacks: they are designed to be invisible to the tools you’ve already purchased and deployed. Checking the box on SCA is no longer sufficient.
What Effective Defense Actually Looks Like
Addressing this category of risk requires capabilities beyond traditional vulnerability scanning and static analysis. Effective defense combines real-time registry monitoring, dynamic mobile application security testing during builds and visibility to actionable threat intelligence that extends beyond CVE-based detection.
Dynamic testing can generate a build-specific Software Bill of Materials (SBOM), enabling teams to quickly identify and isolate affected builds when a new compromise is discovered. This also helps in identifying the developers, build resources and other mobile deployment infrastructure that might require remediation.
Curated threat intelligence for mobile applications provides visibility into supply-chain risks, including vulnerable packages and SDKs that could expose end users, intellectual property and sensitive data, enabling rapid response across affected environments.
Together, these capabilities help reduce the gaps that recent supply-chain attacks have consistently exploited.
From Detection to Resolution: The Remediation Gap
Finding a compromised package is only half the problem. For most organizations, the harder question is: now what?
Security teams need to immediately understand which development machines ran the install, which pipelines were exposed, which mobile builds were potentially affected and which credentials needed to be rotated. Without tooling purpose-built to answer those questions, the scoping exercise alone can take days — days during which an attacker could act on any access they gained.
Orchestrated remediation means that detection triggers an immediate, automated response: pipelines are blocked from consuming the compromised version, affected repositories are identified and surfaced to the right teams and prescriptive remediation steps are delivered in context — rotate these credentials, pin to this safe version, rebuild from this known-good state.
For mobile specifically, this includes mapping the blast radius to understand whether any submitted builds need to be pulled, whether signing keys require rotation and whether a forced update needs to be pushed to users.
Speed matters here in a way that has direct business consequences. The difference between containing a supply-chain compromise in hours versus days is the difference between a contained incident and a regulatory disclosure.
The Stakes Are Clear
The axios attack is not an isolated incident. It follows a well-established playbook that attackers are applying with increasing frequency and sophistication across the open-source ecosystem. What makes it notable is the scale: axios has over 174,000 dependent packages in the npm ecosystem and 100 million weekly downloads — and React Native, which powers roughly 15% of the top 500 most-installed apps, routinely bundles axios directly into the application binary shipped to end users. The number of production mobile apps exposed to this attack window is not a small number. This is a package widely embedded across modern applications, compromised through a single account takeover, using techniques designed to evade many conventional security controls.
For executives responsible for mobile products, the question is no longer whether your supply-chain will be targeted. It is whether you will have the visibility, intelligence, and automated response capability to contain the damage when it is.
The companies that fare best in these scenarios are not the ones with the most tools, they are the ones with the most integrated approach: research that surfaces threats before they go wide, testing that catches what CVE databases miss, intelligence that provides attacker context, and remediation that moves at machine speed.
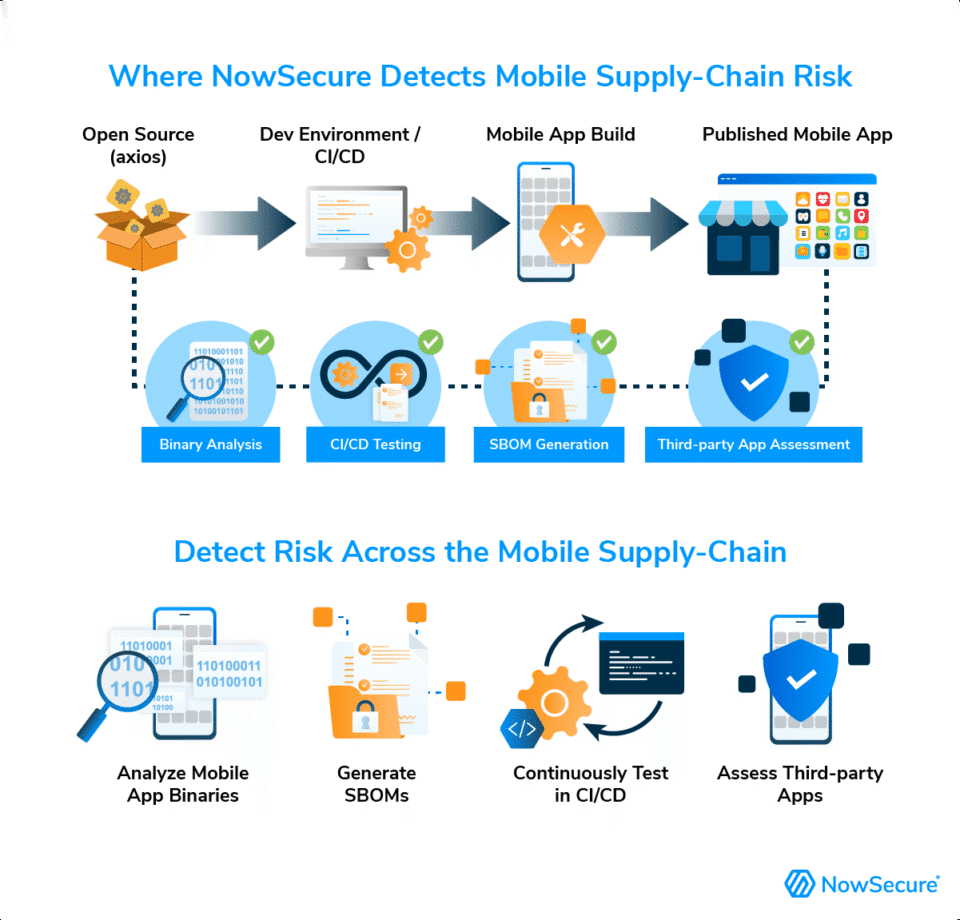
How NowSecure Helps Detect Mobile Supply-Chain Risk
Attacks like axios NPM compromise show how developer ecosystem compromises can cascade into mobile applications and build pipelines. Organizations need visibility not only into source code, but also into mobile apps they build and use.
NowSecure Platform helps security and DevSecOps teams:
- Analyze iOS and Android app binaries
- Generate mobile Software Bills of Materials (SBOMs)
- Continuously test apps in CI/CD pipelines
- Assess third-party mobile apps used by employees or customers
Learn how NowSecure mobile app security testing helps organizations manage mobile application risk.
What NowSecure Customers Should Do
NowSecure Platform users can take immediate action to validate exposure.
- In NowSecure Platform, go to the Apps section in the top menu and locate the application you want to validate.
- Click on the app’s name, find the most recent assessment, and select View Report.
- In the left-hand menu, navigate to Observations, expand the Code Quality section, and click on Software Components.
- Use the search function to filter by each known vulnerable NPM package, and compare the compromised versions with those found in your app.
Your mobile application is only as secure as every dependency it was built with. If you cannot answer the following questions right now, your exposure window is still open:
- Which mobile builds were created from compromised dependencies?
- Which pipelines or developer machines executed the install?
- Which credentials need to be rotated?
Get answers to those questions now. Learn more about NowSecure Platform today.







