Mobile application security refers to the practice of identifying, analyzing and managing the risk associated with mobile apps throughout the software development lifecycle. The discipline encompasses technologies and techniques designed to reduce the impact and likelihood of attackers stealing users’ passwords and sensitive data such as credit card payment information.
Continuous mobile application security testing is a crucial component of cyberdefenses because it enables organizations to find and fix vulnerabilities in the mobile apps they build and use before they release them. Mobile app security testing takes an attacker’s point of view to analyze the security and privacy posture of mobile apps during development or in production. For full coverage, ideally mobile apps should be assessed using a combination of automated mobile appsec testing and manual mobile pen testing.
Why Mobile App Security Testing Is Important
People rely on mobile apps to guide many aspects of their daily lives, from tracking their sleep with wearable devices, to purchasing coffee and checking the train schedule for their daily commute to having dinner delivered and streaming a movie before turning in for the night.
The Apple® App Store® and Google Play™ boast more than 5.4 million apps and counting as of Q1 2022, according to Statista. In addition, mobile apps dominate digital media usage and account for 69% of all digital traffic. Mobile apps have become indispensable to organizationes and are forecast to generate nearly $935 billion in revenue by 2023.
But as the mobile ecosystem grows, so too do the number of threats. Mobile apps have become a rich target for attackers who seek to take advantage of weaknesses in mobile apps to take over accounts, commit fraud or identity theft, access intellectual property, conduct espionage or plant malware.
In the rush to develop new capabilities that improve the user experience and attract new customers, some mobile app developers unknowingly build mobile apps with security and privacy flaws that leak data and put everyone at risk. Personally Identifiable Information (PII) is sensitive data such as a user’s full name, username, email address, phone number, location, account numbers, device ID, device serial number, Social Security Number and more.

Major Mobile AppSec Breaches
Consider these major mobile AppSec incidents. A few years ago, Under Armour experienced the largest mobile breach to date when hackers accessed 150 million MyFitnessPal user accounts. The compromised personal data included user names, email addresses and passwords. That same year, a security flaw within the British Airways mobile app compromised 380,000 customer records, causing a 30% drop in stock value and a regulatory fine of £20 million for violating the GDPR privacy law.
More recently, popular companies such as Amazon, Apple, ParkMobile and Slack all suffered mobile appsec incidents in 2021 and TikTok, Tim Hortons and MyHyundai had mobile data and privacy leaks in 2022. A glance at current mobile appsec and privacy news demonstrates the variety of fintech, mHealth, high-tech and consumer apps that fall victim to poor mobile app security.
And those are only the incidents we know about. Many more mobile apps are vulnerable to security and privacy risks as shown in the NowSecure MobileRiskTracker benchmark tool which shows real-time risk by mobile app categories.
Business Impact of Poor Mobile Application Security
Security breaches can reduce revenue, diminish shareholder value, tarnish brand reputation, undermine user trust and invite lawsuits. For example, a vulnerability in the MyFitnessPal mobile app that allowed threat actors to collect the usernames, passwords and email addresses of more than 150 million customers caused Under Armour to drop 3.8% in market value and eventually led the company to sell off the brand. The Canadian government determined Tim Hortons violated the country’s privacy laws and ordered the company to implement a privacy management program. In addition, Tim Hortons settled a class-action lawsuit about the privacy breach by agreeing to give mobile app users a free hot beverage and baked good.
Mobile app security and privacy vulnerabilities can also subject companies to financial penalties for failing to comply with regulations such as the California Consumer Privacy Act (CCPA), Global Data Privacy Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA). In 2018, the European Union fined British Airways $230 million for violating GDPR after the British Airways mobile app leaked 380,000 credit card payments and personal information. The breach also caused the airline’s stock to drop over 30% and damaged customer relations. And in 2022, the Federal Trade Commission (FTC) fined Weight Watchers International $1.5 million for illegally collecting the personal information of children who used its Kurbo weight loss mobile app.
More recently, the FTC began enforcing its Health Breach Notification Rule and seeking to expand the scope of that regulation. The agency fined pharmaceutical savings app GoodRx $1.5 million for violating the Health Breach Notification Rule after sharing users’ personal health information with third parties. The FTC also seeks to penalize the makers of the fertility mobile app Premon $100,000 for exploiting users via unauthorized disclosure of highly sensitive personal information.
“Because of the differing attack surfaces, traditional web application security testing tools are insufficient for assessing risks in mobile apps.”
Types of Mobile Application Security Threats
Many organizations have mature web application security programs but may lack knowledge about mobile application security basics. It’s important to understand that there are significant differences between web and mobile application security. Mobile apps run on a device typically connected to a cloud and server backend and interact with other apps as opposed to web apps which run on an isolated browser.
Mobile apps have a broad attack surface and many areas of risk. Potential security issues include the following weaknesses:
- Code Functionality
- Development flags
- Stack smashing
- Bad authentication
- Root access
- Path traversal
- SQL injection
- Vulnerable third-party libraries
- Weak cryptography
- Dynamic code loading
- Bad obfuscation
- Unprotected third-party keyboards
- Data at Rest
- Unencrypted sensitive data
- Sensitive data app and log files
- Keychain
- SD card
- World readable files
- World writeable files
- RAM
- Unencrypted credential storage
- SQLite databases
- Secure enclave processor
- Jailbreak/root issues
- Data in Motion
- Man-in-the-middle cert validation
- Man-in-the-middle hostname
- Man-in-the-middle HTTP connection
- Unencrypted sensitive data HTTP
- Remote code execution
- Unprotected zip files in transit
- GPS location leakage
- SSL downgrade
- Unprotected TLS traffic
- Cookie flags
- Certificate validity
- Backend APIs
- Shadow, unapproved APIs
- Improper data routing
- Improperly secured APIs
- Unencrypted communication
- Broken authentication
- Excessive data exposure
- Security misconfiguration
- Improper asset management
Some of the most common mobile AppSec problems include data storage in an insecure, exposed location; improperly coding network calls, insecure authentication or authorization, insecure coding practices and leaving an app susceptible to reverse engineering.
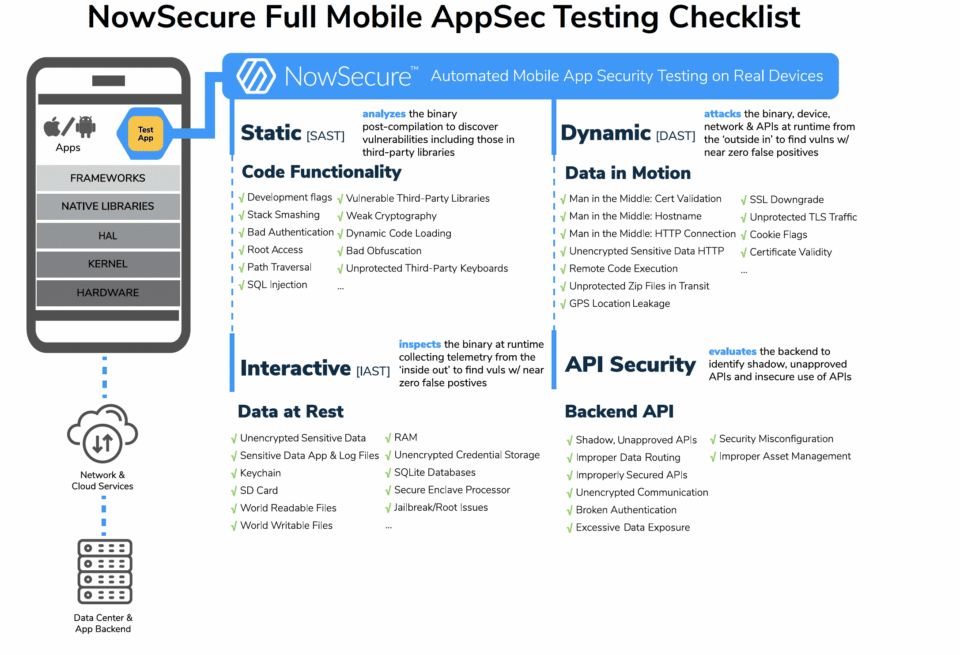
Because of the differing attack surfaces, traditional web application security testing tools are insufficient for assessing risks in mobile apps. Organizations need to thoroughly assess their mobile apps using a combination of SAST, DAST, IAST and APISec testing to uncover security vulnerabilities.
Best Practices for Strong Mobile App Security
Whether establishing a new mobile application security program or enhancing an existing one, organizations should seek to practice security by design. That is, build security into apps from the outset and continuously assess risk throughout the development and deployment phases.
Mobile security analysts and mobile app developers alike can adopt several best practices to strengthen mobile app security and reduce risk. They include the following measures:
- Embrace security standards such as the OWASP Mobile Application Security Project MASVS (Mobile Application Security Verification Standard) and the Software Bill of Materials (SBOM).
- Upskill mobile app developers on secure coding training so they can write more secure apps from the start. NowSecure Academy offers free mobile security training as well as a paid secure mobile development certification.
- Deploy a purpose-built automated mobile appsec testing tool like NowSecure Platform either on demand or directly integrated into the DevSecOps pipeline to quickly assess apps in Dev workflows and return results in minutes.
- Conduct thorough mobile penetration testing for any mobile apps that handle sensitive data or have complexities such as Bluetooth LE traffic, multi-factor authentication or USB connections.
- Continuously monitor mobile apps in production for vulnerabilities or security vulnerabilities that arise from third-party components to safeguard the mobile supply chain.
Founded more than a dozen years ago as a mobile-first and mobile-only company, NowSecure experts have deeply pen tested more than 10,000 apps and automatically tested millions of mobile apps in the public app stores. The world’s most demanding organizations, innovative mobile developers and advanced security teams entrust NowSecure to safeguard millions of mobile app users across banking, insurance, high tech, IoT, retail, hospitality, energy and government sectors.
Contact us today for advice about establishing a mobile AppSec program and obtain a NowSecure Platform demo to see how it can help you scale at speed while ensuring mobile app security and privacy.




