iOS 15 Security and Privacy Updates for Developers and Security Analysts
Posted by Adam Strickland NowSecure Marketing
Apple delighted users and developers alike this summer at its Worldwide Developer Conference (WWDC) by announcing substantial updates to security and privacy. Apple also announced many new features related to design, development and better user experience. Security and privacy features stood out as one of the overarching focus points for the upcoming Apple iOS 15 release this fall.

This article will explore these upcoming iOS 15 security and privacy changes. While some of these examples listed in this article specifically pertain to developers and security analysts, others highlight the exciting new features for all audiences.
Xcode Cloud
Xcode Cloud is one of the most exciting features announced for developers this year. While this may not directly impact security and privacy at first glance, this solution gives developers full integration into Apple’s pipeline for continuous integration and deployment (CI/CD). From developing an app locally to synching in the cloud with your teammates, Xcode Cloud encrypts all data at rest and protects access with two-factor authentication. When your build completes, the ephemeral build environments are destroyed, allowing source code to be accessed only for builds.
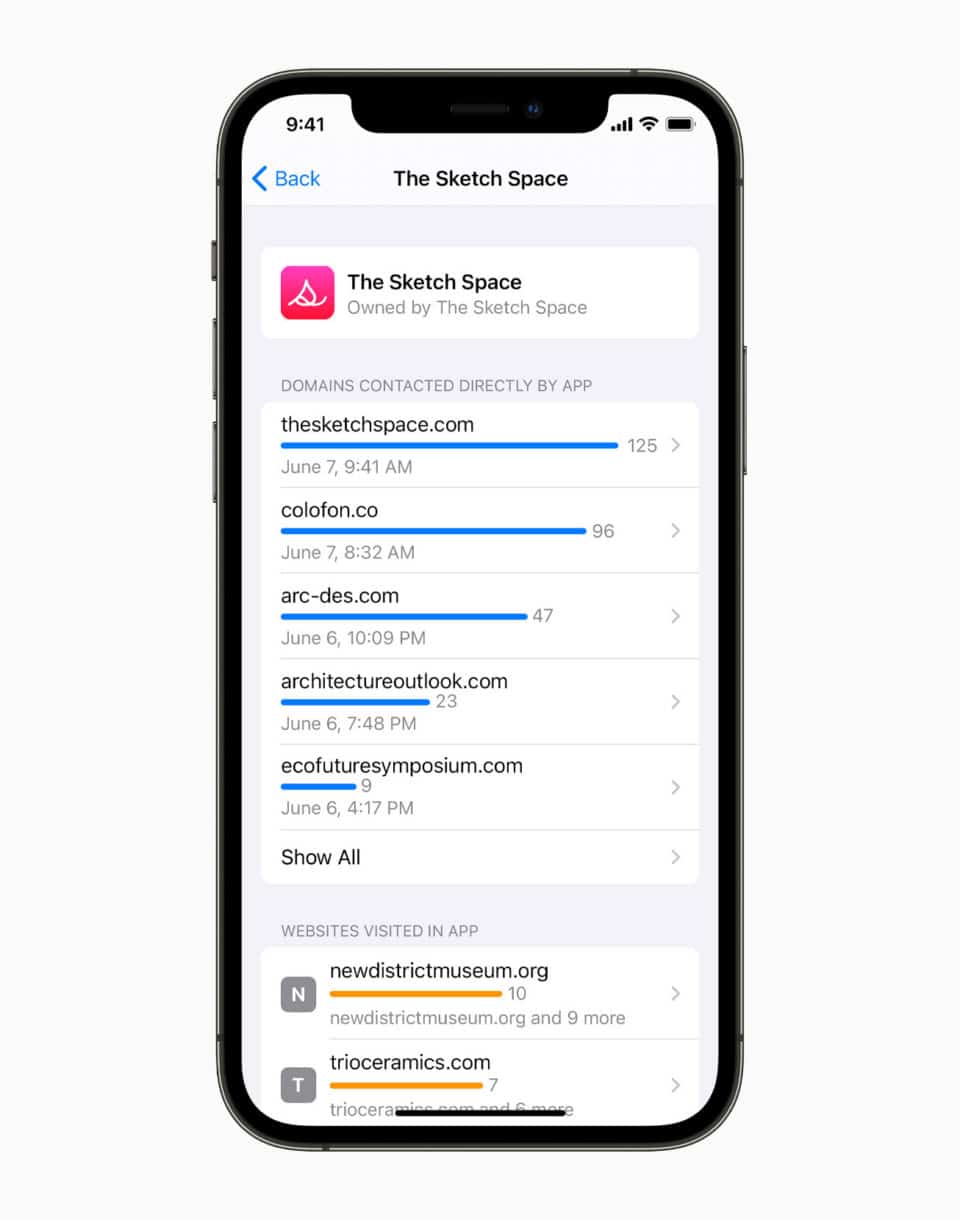
App Privacy Report
Mobile app users will be able to see how frequently each one of their apps has been used with previously granted permission to access sensitive data. The frequency of using this data, such as location, photos, contacts, microphone, and camera, will be fully displayed. This helps highlight if mobile apps are taking advantage of the permissions given. Developers must remain mindful in protecting their users’ data, especially knowing now that data usage will be completely transparent to users. For developers and security analysts, we recommend doing a full network test to check the network calls your third-party dependencies may be making.

Mail Privacy Protection
Mail privacy protection helps hide a user’s IP address and also prevents email senders from seeing analytics of when you may have opened their email. Apple is centering its focus on hiding user identity and online activity, inhibiting IP address tracking and linking to other online activity by routing network calls through multiple proxy services and random IP address assignments.
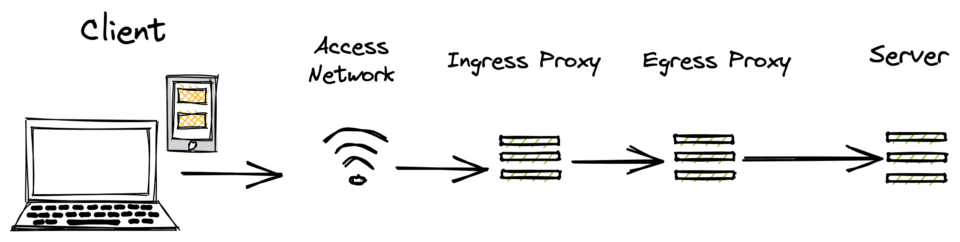
iCloud Private Relay
This is a new service included in iCloud+ that encrypts traffic leaving your device, routing the network connection through two separate internet relays, ultimately connecting the user to nearly any network through Safari. The relay will protect your IP address, location, and browsing history.
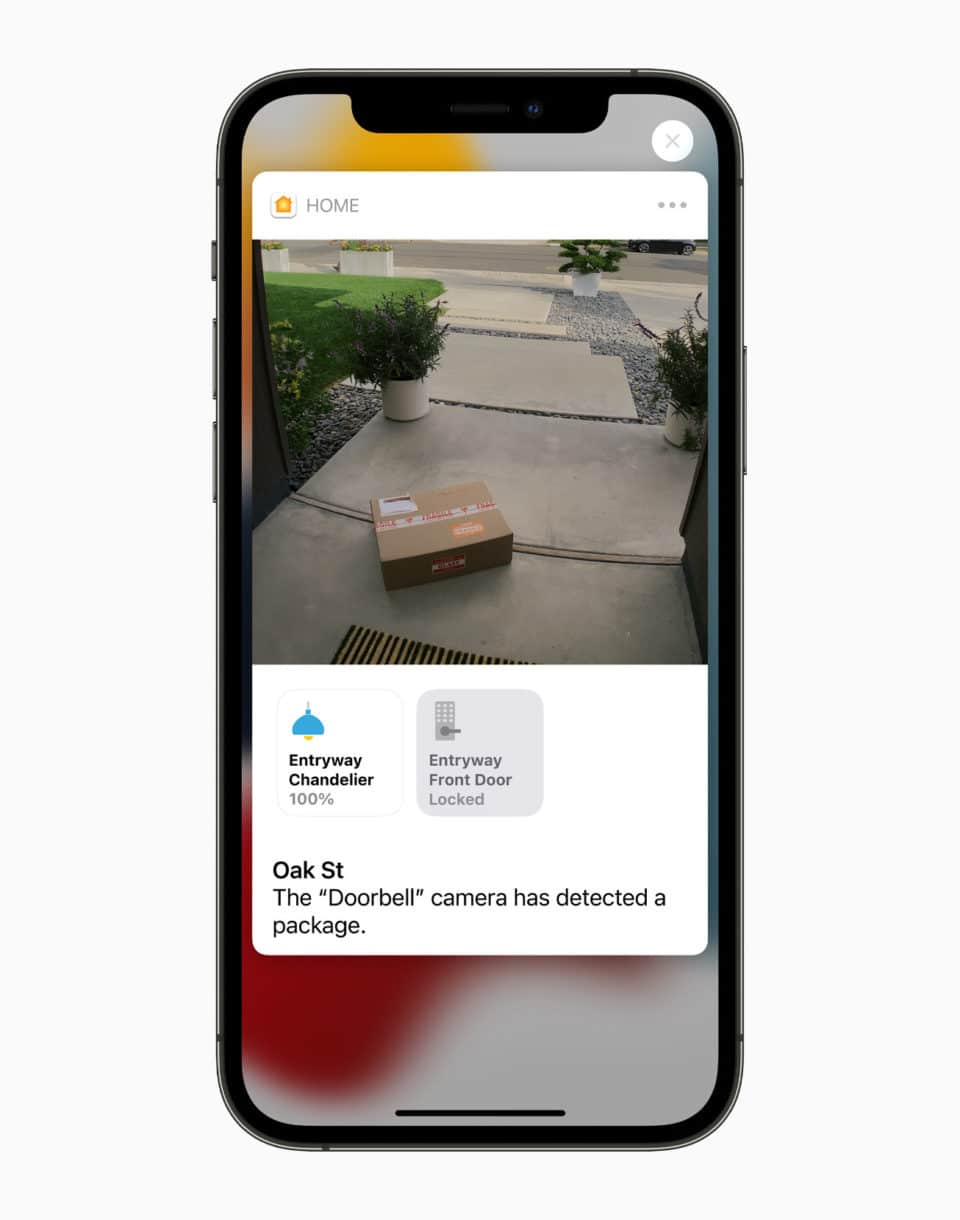
HomeKit Secure Video
Another service built on top of iCloud+, HomeKit Secure Video, will allow the connection of more cameras with end-to-end encryption for transmission and storage. And like the other iCloud services, encryption begins on the device before the data is sent over the wire and stored in the cloud.
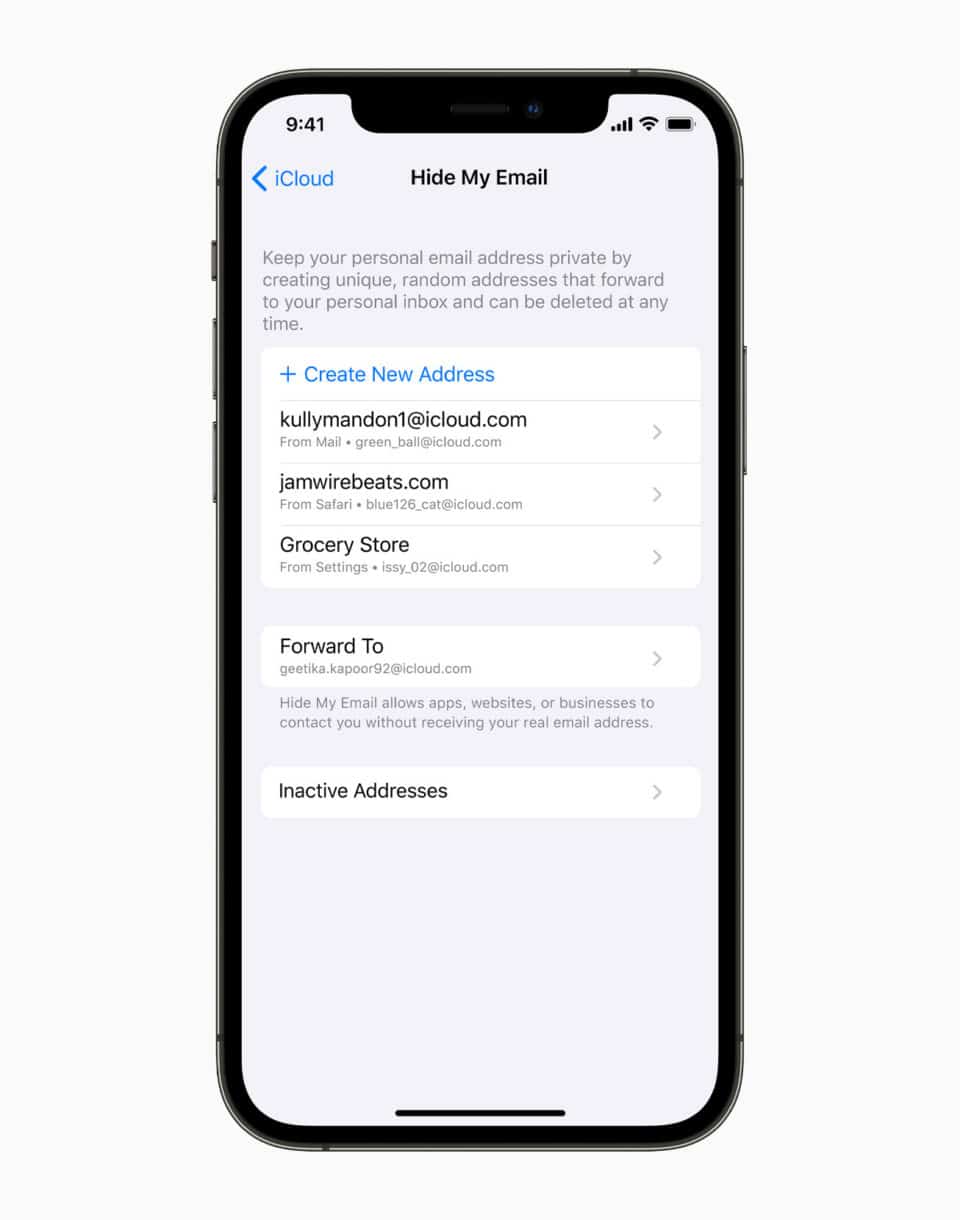
Hide My Email
Have you ever squirmed in your seat by putting in your email address in a website or app? Those days are gone. Users can now generate unique, random email addresses instantly that will forward to your personal email inbox. This feature is built into iCloud Settings, Mail, and Safari.
Audio of Siri Requests:
Now we never need to worry about Siri processing any request off the device and over the network in the backend cloud services because audio of Siri requests will never leave the mobile device. Going forward Siri will perform on-device speech recognition. As a result, Siri will now be able to perform more tasks without any internet connection at all.

Public-Private Key Authentication:
This feature will help register and authenticate users without using passwords, simplifying account creation and authentication. Developers can now begin to dive into the world of a passwordless future. Under the hood: the iOS device, known as the authenticator, sends a public key to the server that it generates at account creation. A private key is also created at the same time.
The server, which is called the relying party, maintains possession of the public key for subsequent attempts and uses assertion to challenge the validity of the authenticator’s identity. There are two methods of this type of authentication: passkeys and security keys. The former pertains to the device storing the public-private key pair through the user’s iCloud Keychain, synching the keys across the user’s devices. The latter stores the key pair on a physical medium, such as a USB key or security card.
The example below illustrates connecting to a service with an existing account.
The first code block starts the assertion request:
var challenge : NSData? // Obtain this from the server.
let platformProvider = ASAuthorizationPlatformPublicKeyCredentialProvider("example.com")
let platformKeyRequest = platformProvider.createCredentialAssertionRequestWithChallenge(challenge)
let authController = ASAuthorizationController([platformKeyRequest])
authController.delegate = self
authController.presentationContextProvider = self
authController.performRequests()
The second code block responds to the request, providing information from the ASAuthorizationControllerDelegate:
func authorizationController(controller: controller, didCompleteWithAuthorization: authorization) {
if let credential = authorization.credential as? ASAuthorizationPlatformPublicKeyCredentialRegistration {
// Take steps to handle the registration.
} else if let credential = authorization.credential as? ASAuthorizationPlatformPublicKeyCredentialAssertion {
// Take steps to verify the challenge.
} else {
// Handle other authentication cases, such as Sign in with Apple.
}
func authorizationController(controller: controller, didCompleteWithError: error) {
// Handle the error.
}
Inspecting Mobile App Activity Data:
Developers and security analysts can now verify that their app accesses only the user data and network resources they expect it to by viewing an exported JSON file. The JSON file contains a series of dictionaries, such as a header, user data and protected resources, marker, and network accesses.
New iCloud CloudKit Instance Property:
Developers and security analysts can now verify that their app accesses only the user data and network resources they expect it to by viewing an exported JSON file. The JSON file contains a series of dictionaries, such as a header, user data and protected resources, marker, and network accesses.var encryptedValues: CKRecordKeyValueSetting
Developers wishing to encrypt new fields in an easy manner through CloudKit will have access to an object that this property returns to read and write encrypted key-value pairs that are stored on the record. The example below shows how to use the new property to encrypt and decrypt a string value:
let record = CKRecord(recordType: "Property")
// Encrypt the name of the property's owner.
record.encryptedValues["ownerName"] = "Maria Ruiz"
// Decrypt the name of the property's owner, using the
// appropriate data type, and assign it to a local variable.
var clientName = record.encryptedValues["ownerName"] as? NSString
New Core Data Instance Property:
var allowsCloudEncryption: Bool {get set}
If developers would like to store an attribute’s value in an encrypted form in iCloud, simply set this property to true. You can also set this in the Core Data model editor using the Allow Cloud Encryption attribute in the Attributes inspector.
App security and privacy took center stage at Apple’s developer conference this year and remains the pivotal factor in Apple’s success. We saw many companies this year exceed the status quo in security for both users and developers. We can absolutely assume that users will welcome these iOS 15 updates with open arms, developers will have more protection in their apps, and security analysts will appreciate the new functionality while having more to test.
Be sure to check out how your dev team can become security all stars with the NowSecure secure mobile app development training.






