The recent SolarWinds supply-chain attacks demonstrate the need to focus on the entire IT landscape and underscore the risks posed throughout elements of the supply chain. All enterprises and federal agencies use commercial mobile apps and therefore are exposed to risks of mobile app supply-chain attacks, yet few are protected.
Mobile apps have become the new gateway to the enterprise and should concern executives, organization leaders, and security, risk and compliance professionals. As a best practice, all organizations with users, customers and data should continuously monitor their mobile app supply chain for security, privacy and compliance risks.
The mobile app supply chain includes more than 6 million mobile apps publicly housed in Apple App Store™ and Google Play™ plus millions more custom mobile apps provided by vendors or built by outside consultants.
- More than 130 billion mobile apps were downloaded in 2020
- 69% of all digital time is spent in mobile apps vs web apps
- Mobile users have an average 60 – 80 mobile apps on their devices
- Each human has an average of 1.5 devices
- The 1,000 most popular apps typically update daily, weekly or bi-weekly, making risk prevention a moving target
- Mobile app breaches are increasingly common — check out this long list of security and privacy incidents.)
Massive Mobile Attack Surface in the Supply Chain
It’s clear that the mobile app supply chain presents a massive attack surface and risk to users, organizationes and agencies alike. And the scope can be dramatic. For example, one of our customers has over 18,000 mobile user devices with 12,000 distinctly different mobile apps and versions. That’s 12,000 points of risk to the enterprise, many of which are updated monthly, weekly or even daily.
Examples of Mobile App Supply-Chain Incidents:
- Snyk researchers discovered SourMint was a Malicious Chinese SDK from Chinese ad network Mintegral to harvest data and redirect users. The ad SDK for years functioned properly and used by thousands of developers, then was suddenly updated with malicious code. NowSecure identified the malicious ad SDK in more than 1,200 iOS apps in production with billions of installs.
- Attackers cloned the BarcodeScanner Android app, added malicious code to redirect to custom ads, uploaded the imposter app to Google Play looking like the original, then infected thousands via Google Play downloads.
- NowSecure researchers discovered the Vungle advertising library incorporated into apps used by millions of users that contained an arbitrary write vulnerability that enabled remote code execution on Android devices.
- NowSecure researchers found the Vitamio Multimedia SDK used by thousands of published applications to play media files enabled a world writable directory with world writable files that could be exploited for remote code execution and privilege escalation through permission stealing, as recognized by Google.
- NowSecure researchers discovered that the Corrupdate supply-chain vulnerability impacted Samsung Account and GALAXY apps on more than 100 million devices. The vuln allowed an adjacent network attacker to replace an official Samsung app update with his own malicious apk.
- NowSecure researchers found a vulnerability in a popular Android ad library enabled an attacker on the same network to write files into the app context, such as via a malicious Wi-Fi hotspot.
Inside Breaches with MITRE ATT&CK
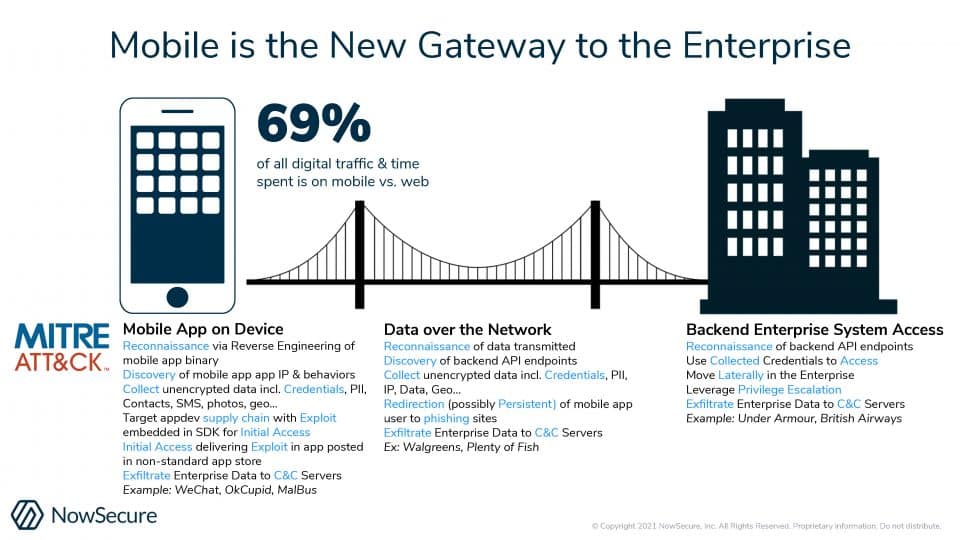
A growing community of attackers has learned how to exploit the myriad of vulnerabilities found in mobile apps and the mobile app supply chain. Using the MITRE ATT&CK framework for iOS and Android, mobile apps are used to attack the enterprise in three ways as shown in the graphic below:
- Attack the mobile app on the remote device
- Attack mobile app communication over the network
- Attack the back-end enterprise systems
From reconnaissance, discovery, data collection, deployment of exploits, penetration of backends, and lateral movement to exfiltrate enterprise data, mobile apps present as much or MORE risk than web and network attacks. And more often than not, the enterprise remains unaware and unprotected.
Protecting the Mobile App Supply Chain
To mitigate risk, organizations should perform continuous vetting for mobile app security issues when mobile apps are first requested for use and for changes each time mobile apps are updated. Common risks and attacker exploits include:
- Leaking credentials that could be used to penetrate the back-end and move laterally through the network;
- Insecure back-end APIs that can be exploited to penetrate the back-end and move laterally through the network;
- Improperly validated connections that could redirect users to phishing sites;
- Wide-scale leakage of personally identifiable information (PII), geolocation, telemetry and other critical data.
Only continuous vetting of mobile apps enables organizations to block high-risk mobile apps from use to protect the enterprise from mobile app supply-chain attacks.
The NowSecure Supply Chain Risk Management solution enables organizations to inventory and triage the risks in their existing mobile app portfolio and then continuously monitor all mobile applications throughout the enterprise.
Learn more about how NowSecure helps protect the mobile app supply chain through the U.S. Department of Homeland Security (DHS) Mobile AppVet program in this upcoming webinar and read the U.S. Marshals Service in this case study.