Just in time for the OWASP Global AppSec 2020 virtual conference, mobile app security analysts and developers have a new app with which to test their reverse engineering skills. As a proud sponsor of the OWASP Mobile Application Security Project and the Global AppSec conference, NowSecure researchers and r2 community members helped develop and maintain the Android Radare2 Pay v1.0 crack-me app featured in the OWASP Mobile Application Security Testing Guide (MASTG).
The MASTG serves as a reference guide for security analysts of all levels to learn how to test areas of the OWASP MASVS on Android and iOS apps. With the addition of the new Radare2 Pay app, the MSTG now includes four Android apps of varying levels of difficulty. This one is compatible with Android 4.4 and above, although it’s recommended to be installed on devices using Android 9.0 onwards.
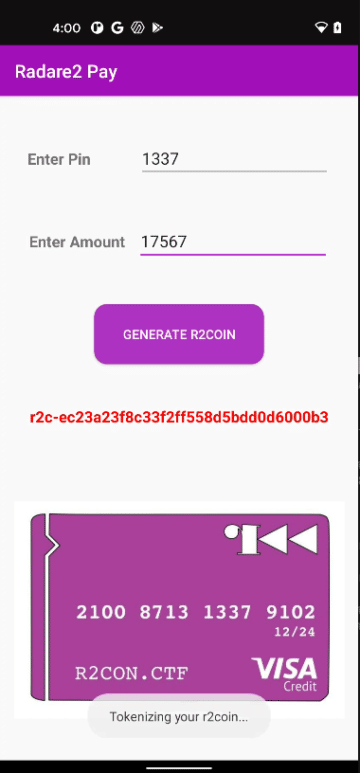
Building on the open-source tooling work of Frida, Radare and r2 communities founded by NowSecure researchers, Eduardo Novella of NowSecure and fellow researcher Gautam Arvind created a payment app crack-me for the OWASP MASTG modeled after an app that would enable the r2 community to make payments and transfer money between users. They previewed the Radare2 Pay app as a challenge for the CTF competition at the virtual r2con 2020 event.
 |
 |
Intended to be similar to popular mobile payment applications such as Google Pay, the Radare2 Pay app is difficult to crack. It features layers and layers of obfuscation and protection and anti-rooting technology in order to delay attacks. The developers used white box cryptography and created their own version of Runtime Application Self-Protection (RASP) with anti-Frida protections to make it harder to recover the payment keys.
Novella estimates it took the pair about two or three weekends to develop and test the app. Because Arvind is based in Singapore and Novella in Spain, they worked through the challenge of collaborating from differing time zones.
“We took the master key and merged it in tables in such a way that it’s very unlikely the attacker will uncover the key,” says Novella. “In order to frag the key, you need to have some insight into side channel attacks and cryptography. Frida cannot recover this key but it can help to trace through layers of obfuscated code.”
Only one person solved the challenge at r2con who works in the mobile space and the whiteboxed master key was not recovered. After the Radare2 conference, Researcher Romain Thomas published a two-part solution showing how to defeat the RASP protections and performing fault-injection attacks against the whitebox cryptography implementation to recover the obfuscated master key buried in the binary code. (See Part 1 and Part 2).
“Creating challenging apps like this one by Arvind and Novella is a great way to push the envelope for both automated and manual mobile application security testing,” says NowSecure Chief Technology Officer David Weinstein. “We’re excited to see the OWASP embrace the application and proud to continue contributing to the open-source community.”
Meet Novella and other NowSecure researchers and learn about open-source tools from NowSecure researchers at the NowSecure Connect 2020 virtual conference on Nov. 17. Register here to join.