Known in the security community as Hex (@Hexploitable), Grant Douglas helps build and enhance the NowSecure automated mobile application security testing solutions. Prior to joining the NowSecure research team in 2020, he directed mobile security services for a consulting company.
Known in the security community as Hex (@Hexploitable), Grant Douglas helps build and enhance the NowSecure automated mobile application security testing solutions. Prior to joining the NowSecure research team in 2020, he directed mobile security services for a consulting company.
Douglas spent the past eight years performing security assessments of mobile apps and has hundreds of pen tests under his belt. He holds a degree in ethical hacking and countermeasures from Abertay University in Scotland. He recently spoke with us about the different perspectives in that offensive work versus the research he tackles today for NowSecure.
Q: How long have you worked for NowSecure?
A: About 5 months now — I started in May.
Q: Why did you join the company?
A: Mobile security has been my focus for the last few years and NowSecure is very well known in this space, particularly for its commitment to open-source tools such as Frida, Radare and r2frida. Having used these tools, spoken to members of the research team and witnessed the power of NowSecure products, joining the company was an easy decision.
Q: What do you do as a mobile security research engineer?
A: Our job is to innovate to make our customers more successful, which can range from researching the new gotchas in upcoming Android and iOS versions to autonomously surfacing more vulnerabilities, or new ways to drive analysis of an application. Everyone is trying to figure out how to make our solutions faster, better, more accurate and inject value for the customer.
Q: How does your previous security consulting experience differ from mobile application security research?
A: Most of my consulting work consisted of manual source code review and penetration testing of mobile apps, desktop apps, web apps and APIs. You wear the hat of a malicious actor to find and exploit vulnerabilities deep within software and help developers fix them.
Now I still try to figure out known problems and things that can go wrong, but empathize and wear the hat of the developer. We need things to work the way development teams want to work. When we scan apps, people want fast, accurate results; they don’t want false positives or 12 day assessments of every subtle application change.
The biggest challenge for me was that in consulting, you have very clear goals. Say you review a banking app for three weeks, you find a bunch of problems, you write a report. The outcome is clear and tangible. But in research, you’re looking at something that may or not be possible. The conclusion might be that it’s not viable – and that’s ok. You are often looking at areas never documented or explored before.
Q: Do you specialize in a particular mobile operating system?
A: I can work with both Android and iOS platforms although the more advanced security stuff I’ve done in the past relating to obfuscation and Runtime Application Self Protection (RASP) is iOS focused. I find that iOS is more interesting for me.
Q: What mobile application security testing tools do you use most?
A: My most frequently used tool at the moment is Frida, and second to that is Radare.
Frida is a dynamic binary instrumentation framework that allows you to essentially debug a process live, with a rich API for doing complex analysis such as recording functions that run, the order of which they run, the arguments passed to functions and the values returned by a function call. You can inspect all of the libraries, functions and classes loaded in the process, and you can trace all of that code too. There’s lots more to Frida, so if you haven’t tried it yet, you should definitely go check it out.
Radare2 (r2) is an open-source reverse engineering toolkit available for multiple platforms and architectures, providing quick insight into an application and its inner workings. R2 can be used to review the strings, classes, functions, disassembly and decompilation of the app, amongst many other features.
It’s not just because I work at NowSecure — these tools are open source and widely used by the mobile security community. They are truly awesome. I’ve also been using Microsoft’s Visual Studio Code as my text editor to write my Frida scripts in TypeScript which gives you types, tab completion and more. It’s a really nice way of working. See my colleague Ole’s handy template to get started.
Q: What OSS tool did you develop?
A: In the past I worked on a tool called Memscan that lets you search inside an app’s memory. Let’s say you’re looking for encryption keys or passwords inside the app. Tools like Frida and Substrate can do the same thing, but the target app can detect their presence and change its behavior. Memscan doesn’t actually go inside an app, it does it from afar. Essentially, I wanted to be able to stealthily inspect an app’s memory. But there are now creative ways to do that with Frida so Memscan hasn’t been updated in a long time.
Q: How did you use NowSecure solutions in your previous roles?
A: In my previous role, I used the NowSecure Workstation kit to speed up pen testing. At scale you’re doing hundreds and hundreds of mobile assessments and if your team has varying levels of knowledge and skills, Workstation enables you to complete foundational coverage in just a few hours to take care of the easy stuff automatically and then lets you go deep and perform interactive testing of the more tricky and advanced stuff. It’s a good way to enable senior and junior consultants to collaborate together and come up to speed on mobile security.
A client of my prior consulting organization also had me Iook into NowSecure Platform, an automated mobile app security testing solution. Platform is very good at routinely scanning and identifying problems for baseline testing whereas Workstation allows you to test the app in more creative ways.
Q: What other aspects of mobile appsec interest you?
A: Runtime Application Self Protection (RASP) is quite fascinating. They typically come in the form of commercial products which are built into apps to guard against reverse engineering and tampering. Amongst other things, they’ll look for Frida, they’ll check for evidence the device is jailbroken and randomize their behavior to make it difficult to pinpoint exactly what’s going on. I’ve helped people in the past make the best use of these products and analyzed their effectiveness by trying to circumvent them.
I also like to explore analytics and metrics. To say we have a lot of data at NowSecure is an understatement. We have data on millions of mobile app assessments. I like to look at the different perspectives that we could draw from the data and think of different ways of analyzing it to see which apps might be affected by a problem that comes up in the wild.
Q: How have you participated in the R2con conferences?
A: I spoke about mobile security app hardening (RASP things) at r2con 2019 and alongside my colleague Eduardo, I ran a full-day advanced r2Frida workshop. I had already worked with Edu in the past and met other NowSecure researchers at the conference. This year I didn’t speak at the virtual r2con 2020 event, but helped run a basic introductory workshop that covered how to set up r2Frida, the fundamentals and how to use it to do reverse engineering. It was a really good event and remains online for anyone who wants to go follow along with the recording.
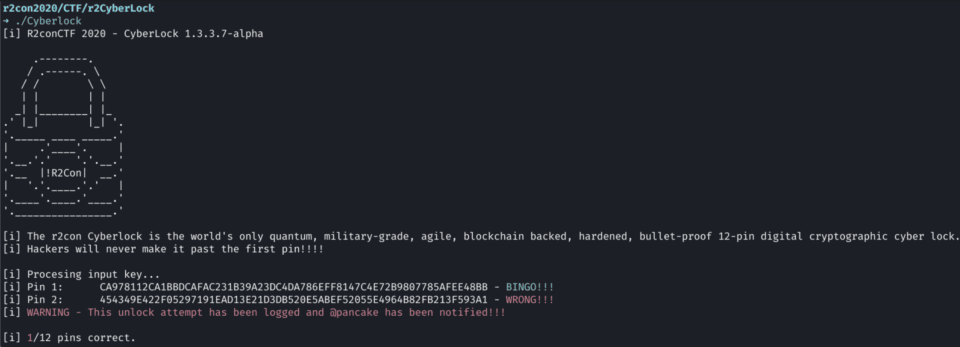
I also built a fun challenge called Cyberlock for the Capture the Flag competition that only a few solved. Whereas in some crackme challenges there’s a quick path to victory, this required quite a bit of problem solving.
CTFs are very fast paced and you’re competing against the leaderboards. You’ve got the added pressure of people catching up in points so sometimes you give up on problems and move to the other ones because you don’t want to waste time. This is probably why it didn’t have too many solves but I’d encourage anyone interested in reverse engineering to go give it a try, and if you’re new, check out the solutions and try it yourself.
Q: What personal mobile device do you use, an Android or iPhone?
A: I have an iPhone XS — I didn’t upgrade last year but I’ll hold out for the 12 this year I think.
Learn more about a few of Grant’s fellow researchers in Q&A discussions with Rono Dasgupta, Dawn Isabel and Francesco Tamagni. And stay abreast of the latest mobile DevSecOps news by subscribing to our twice-monthly newsletter.