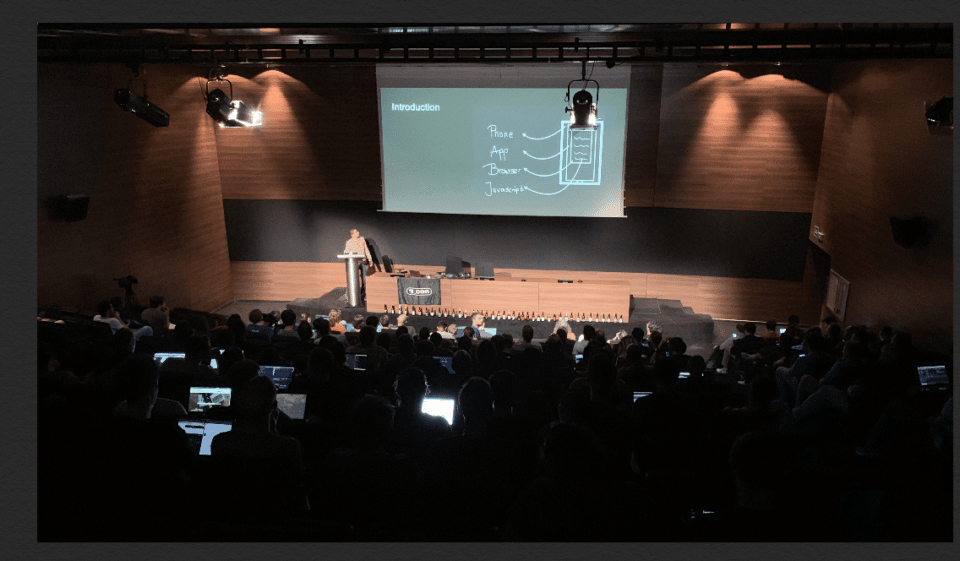
In early September, radare2 users and developers from around the globe gathered in Barcelona for r2con, an annual conference celebrating the r2 multi-platform, open-source, reverse engineering framework supported by NowSecure.
Around 200 attendees enjoyed four days of hacking, teaching, discussing, coding, socializing and having fun. Taking the usual format, the community-driven event featured two days of training followed by two days of 18 conference sessions focused on reverse engineering, open-source software development, forensics, software protections, exploiting, vulnerability research, malware analysis, mobile application security and more. The event also featured Frida, another popular open-source tool sponsored by NowSecure that can be combined with radare2 thanks to the NowSecure-developed plugin.
“R2con is by far the most friendly security conference that I’ve attended,” says Eduardo Novella, a NowSecure mobile security research engineer. “It has always been impossible to skip it since the first edition. Technically speaking, there’s no doubt whatsoever the reversers there are insanely smart! The atmosphere was outstanding.”

A trio of NowSecure mobile app security researchers Eduardo Novella, Francesco Tamagni and Ole André Vadla Ravnås listen intently. Ravnås was inspired to develop a new Frida API during the conference.
This year, the five training workshops were organized by the degree of experience on r2 — introductory and advanced. Both training tracks ran in parallel in different rooms before the conference. Advanced training sold out fairly quickly, which demonstrates that r2con attendees are highly skilled reversers, notes Novella, a contributor of APKiD.
Two of the trainings were taught by NowSecurians (Advanced Mobile App Reverse engineering with r2frida (Eduardo Novella of NowSecure and Alex Soler and Grant Douglas), and “Developing Internals” (Sergi “Pancake” Alvarez, the author and main developer of radare) covering how to modify, improve, fix and extend the internals of the radare2.
Technical Learning
Regardless of the level of training, the talks were generally quite detailed and technical. (You can find the slides to most of the sessions here.) The attendees enjoyed the basic and advanced trainings, but condensing the material into two days was a challenge. The most common request organizers fielded was to lengthen the training workshops to two to four days.
In no particular order, here are some of the highlights of the r2 training and conference sessions:
- Mobile Reverse Engineering with R2frida (Eduardo Novella of NowSecure, Alex Soler and Grant Douglas): This training was focused on mobile reverse engineering using r2frida, an r2 plugin that blends the best of Frida and radare2. The trainers covered topics such as SSL pinning, malware unpacking anti-jailbreak, anti-debugging and even anti-Frida. All these security protections were suitable to be tackled with r2frida. Exercises were offered as crackmes and run within mobile emulators for the students.
- Advanced Techniques for Semi-automatic Code Deobfuscation (Tim Blazytko): This workshop covered the latest state-of-the-art techniques on code (de)obfuscation. Blazytko mainly showed theory and exercises about code obfuscation such as opaque predicates, control flow flattening and VM-based obfuscation. The practical part leveraged the reverse-engineering framework miasm2 and symbolic execution feature to convert the obfuscated binary code into an intermediate language (IL) which allowed him to undo the flattening and get rid of opaque predicates. This proved that heavily-obfuscated control flow graphs can be highly simplified using symbolic execution.
- Cutter (Antide Petit, Itay Cohen and Florian Märkl): In addition to showing off this amazing user interface for radare2, the session presenters unveiled the brand new full-fledged integration with the Ghidra standalone decompiler. Being loaded as part of the very r2 process, advanced integration is possible. The propagation of r2’s type definitions allow for good results, making decompilation actually useful.
- Who you gonna’ syscall: using automation to analyze protected iOS apps (Grant Douglas): Douglas demonstrated bleeding-edge techniques and common pitfalls for analyzing apps which are packed with “protectors,” especially those using inline assembly syscalls to perform anti-jailbreak and anti-frida checks. It focused on automating bypassing those protections by using r2pipe, r2frida and Frida, and even explored the usage of Frida’s Stalker to achieve that in a stealthy way.
- radare2 and Frida in the OWASP Mobile Security Testing Guide (Carlos Holguera): This session offered a nice introduction to the MSTG, with live demos in r2, Frida and r2frida. It provided a good starting point for those interested in bootstrapping their skills for mobile app security testing, but was also useful for seasoned researchers interested in contributing to improve the guide and the proposed techniques and tools.
- TEB/PEB/../DLL binary Blob for ESIL to parse (Dennis): The presenter showcased how he emulated the weird and stealthy initial steps a Windows malware sample has taken to resolve the system APIs that it needed. What’s astonishing about this talk is how malware researchers are calling for ESIL improvements needed to prepare against malware implementing ESIL detection or anti-ESIL techniques.
- ELF Crafting. Uncovering Advance Anti-analysis techniques for the Linux Platform (Nacho Sanmillan): This presentation exhibited techniques to reveal malware on Linux OSes. Internals about the ELF format were explained in detail to understand the wild tricks that actual malware is employing out there. Finally, Sanmillan showed us more ways of action for advanced malware that we could see in the near future.
- R2learn (Sergi ‘Pancake’ Alvarez of NowSecure and ki): This talk covered two different ways to learn how to use radare2 and assistance remembering the commands. And introducing some gamification into the framework.
- Down the organization with r2dwarf (Giovanni Rocca): Mobile security researcher @iGio90 presented his cross-platform r2frida front-end in python-qt, which aims to provide a debugger interface on top of Frida with support for breakpoints and scripting in Python and JS with some higher level concepts compared to Frida.
- A journey through ESIL (Arnau Gàmez i Montolio): This talk by @condretleveraged the r2’s intermediate language ESIL to be used for drawing function-scoped control flow graphs and reducing garbage to optimize the logic at the microcode level. It exposed some tricks to improve the analysis by making static analysis out of the emulation engine.
- Object Diversification (Alex Gaines): Gaines used r2 to mutate binaries in order to add more entropy in order to complicate attackers and analyzers when trying to exploit vulnerabilities. Changing the way the code is structured, the stackframe size, function boundaries, etc make life harder for hackers.
- Me and You everyone we debug (anonymous): This good talk covered a useful new debugging backend plugin based on the PIN framework, which also adds the ability to do timeless debugging with r2.
Friendly Competition
Part of the fun of r2con was taking on the challenge of the competitions:
-
- Contributions: The purpose was to find bugs in r2 and improve it by adding new functionalities or enhancing existing ones. The most important contributions were the panels interface, ESIL graphs and added support for the AMD29K CPU which is still widely used in printers.
- CTF: Offered a week before the conference, players competed to solve different kind of challenges based on several architectures. More than 300 people registered and one- third scored points.
- PwnDistro: The purposes of this competition was to find and publish a vulnerability in r2 (and reproducer) that is present in all the distributions. The fix appeared in the release after (r2-3.9) – the winner’s blog post is worth a read.
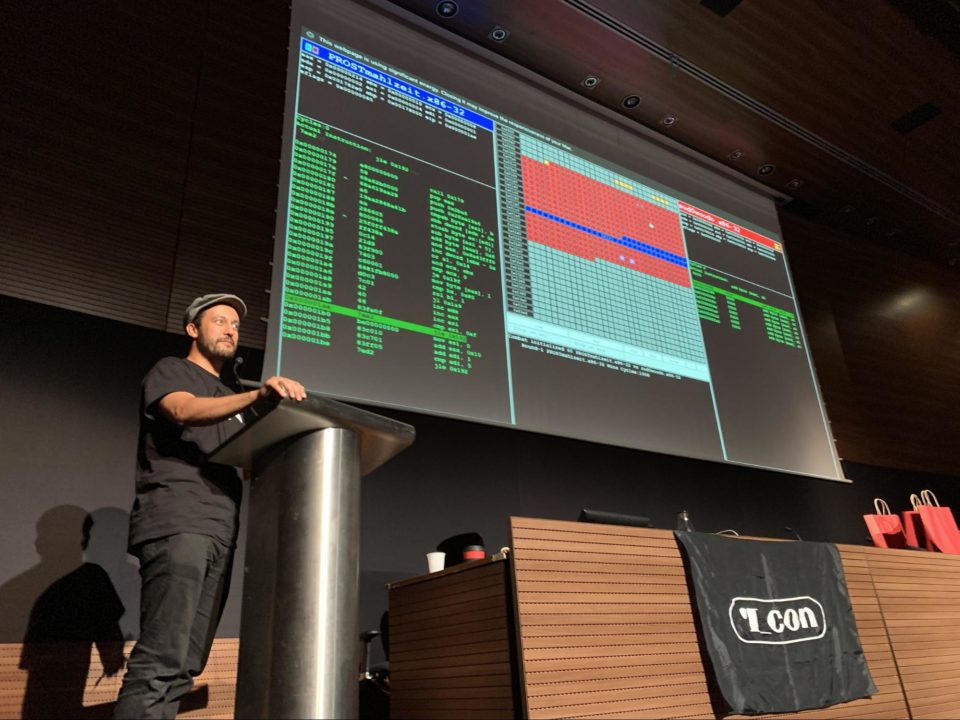
- R2wars: following the success of previous editions, we decided to run the r2wars competition once again. This game is similar to corewars, but running on top of radare2, using the esil emulation engine to allow multiple programs written for MIPS, THUMB, ARM32, ARM64, X86-32 or X86-64 to run in the same memory space in order to make the others crash, the hidden purpose of this game implies improving the emulation support for those architectures, add more instructions, find and fix bugs and exploit design issues if any. The winner of this edition wrote an extensive blog post which explains the techniques used and the rules of the game
- RSoC: NowSecure sponsored the Radare Summer of Code to improve the user interface and interaction features of r2.
Winners scored great prizes and swag including a game console running Linux (it also runs r2), printed copies of the r2 book, flags with the radare logo, mouse pads and nose pads.
All attendees scored a backpack and reusable r2 mug.
Food and Fun
The event fee of about 80 euros included free coffee, juice and beer, and a pizza party on the last day. Speakers received complimentary access to all trainings as well as a special dinner, and assistants had access to an abundance of vegan food.
“The friendly nature and expertise of all the attendees and speakers made for many informal and spontaneous sessions where everyone was eager to share tricks and techniques with others over a beer,” says NowSecure Mobile Security Research Engineer Francesco Tamagni. “This was very valuable and pretty unique and I learned a lot as usual.”
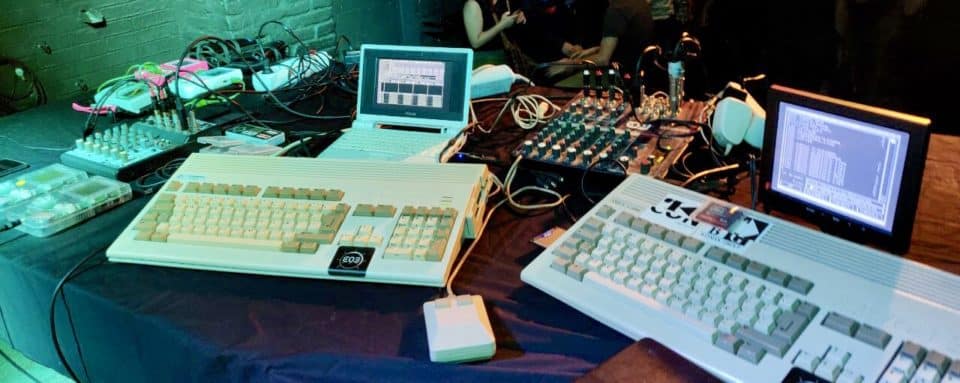
Friendly members of the open-source community enjoyed great spontaneous conversations and shared tips and techniques over a beer. Finally, R2con conference goers celebrated the end of the conference with a chiptune party featuring music made on Amiga and Gameboys by @neuroflip, @cyanidedansen and @the4dboy.

A good time was had by all and everyone learned from one another. We hope you can join us in 2020. “If you’re into reverse engineering, the conferences REcon and R2con are definitely a must,” recommends Novella.
In the meantime, please consider engaging with the radare community to learn more about the tool and reverse engineering in general and contribute to it.