A 3-Part Mobile App Security Testing Checklist to Build Your Program
Posted by Brian Reed NowSecure Marketing
While web app security testing is an established practice, mobile app security testing throws more complex challenges at security analysts and developers. Recognizing the substantial differences in risks and vulnerabilities between web and mobile apps, OWASP crafted a separate OWASP MASVS. However, our NowSecure analysis of third-party apps in the Apple® App Store® and Google Play™ store shows that some 85% of mobile apps still violate one or more of the OWASP mobile Top 10.
To help security analysts and developers craft a more effective list of mobile testing requirements, we’ve assembled a Mobile App Security Testing Checklist of three key questions to address that you can download here.
1. What types of testing do I need?
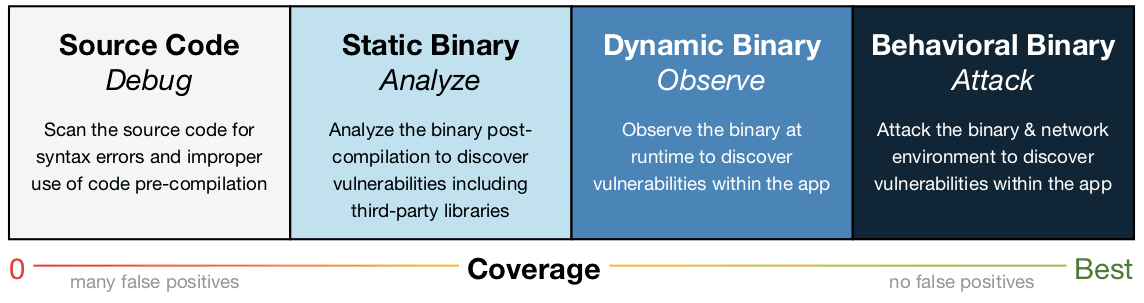
Static testing in reality only analyzes source code and misses 70-80% of actual real-world issues found in real applications. Therefore effective and efficient mobile appsec testing programs require tools that also provide dynamic and behavioral testing to ensure comprehensive coverage with nearly zero false positives.
2. What testing coverage do I need?
Look for complete coverage on the device and over the air, not just the code itself.
- Data at Rest: Testing for sensitive data such as account credentials, personally identifiable information (PII), email addresses and more insecurely stored in SQLite databases, log files, plist files, XML data stores or manifest files, binary data stores, cookie stores, and/or SD cards.
- Data in Motion: Testing for sensitive data such as account credentials, PII, email addresses and more insecurely transmitted due to SSL/TLS certificate issues, poor handshake or HTTP transfer of data in cleartext.
- Code Quality: Testing for code security issues such as buffer overflows, format string vulnerabilities, SQL injection, arbitrary code execution, and other exploits resulting from using the wrong API, using an API insecurely or using insecure language constructs.
3. What testing requirements do I need?
To be most effective, testing tools should use industry-standard approaches and integrate into your existing tools and workflows.
- All tests should be run on real iOS and Android mobile devices—not emulators—to ensure complete real-world coverage and accuracy.
- Findings should include industry-standard CVSS Scores, remediation instructions and mappings to OWASP MASVS.
- Testing software should integrate into the development toolchain, including build systems such as Jenkins, ticketing such as Jira and repositories such as GitHub.
Putting it all together
While mobile app security testing may be new to many, it’s an essential component of risk management. Security analysts and developers alike benefit from high quality, repeatable mobile app security testing programs. To design your organization’s program and choose the right tools that best meet your needs, consult our helpful Mobile App Security Testing Checklist.





