New Year’s resolution for iOS developers? Support App Transport Security (ATS)
Posted by NowSecure Marketing
Exercising more frequently? Eating healthier food? Saving more money? What self improvement endeavors have you committed to in 2017? For the good of your organization and customers, add one more resolution to your list — pumping up the security of your iOS apps by supporting App Transport Security (ATS) to create a more secure, and therefore higher quality, customer experience.
What is App Transport Security (ATS)?
App Transport Security (ATS) is an iOS feature that forces mobile apps to connect to back-end servers using HTTPS, instead of HTTP, to encrypt data in transit. ATS enforces a minimum security level for communications between a mobile app and web services that support its functionality. Software development kits (SDKs) for iOS 9.0 or later enable ATS by default, but developers can opt-out by setting an app’s NSAllowsArbitraryLoads key to True.
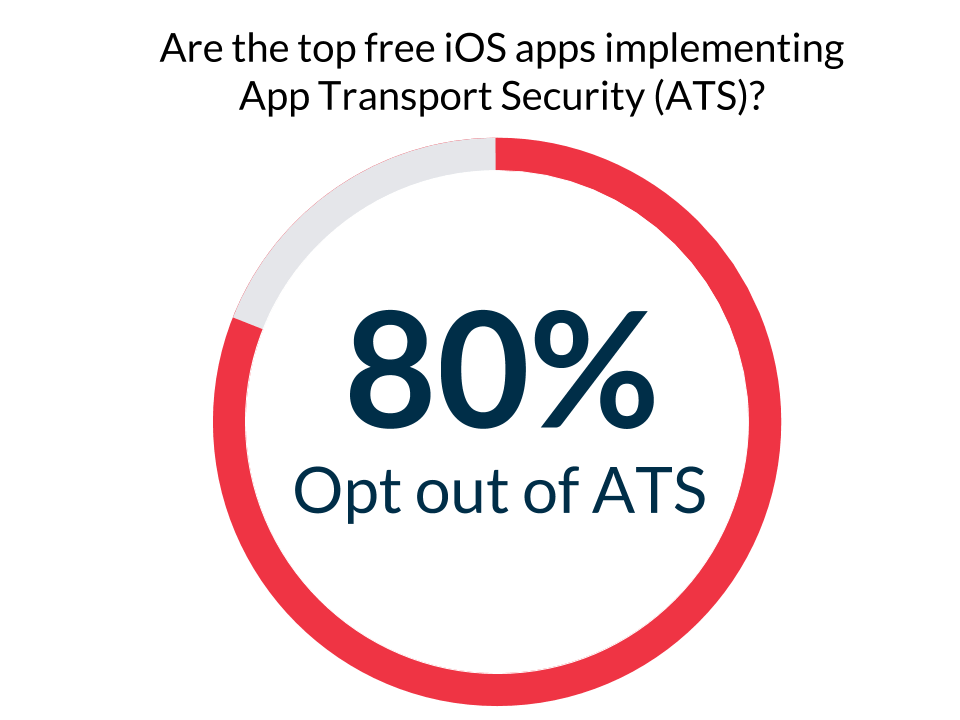
Unfortunately, an analysis of the most popular free iOS apps on the App Store suggests that a majority of developers disable ATS. Many developers opt out based on instructions from their ad library provider and don’t realize the consequences of doing so.
Back in August, NowSecure Director of Research David Weinstein discovered that 80 percent of the top 50 free iOS apps on the App Store had disabled ATS.
This week David expanded his sample size and assessed 201 of the most popular free iOS apps. He found that no progress has been made over the past five months (see below for details of David’s analysis). In other words, a great many iOS apps may be transmitting sensitive data insecurely.
When is the deadline for implementing ATS?
At its World Wide Developers Conference (WWDC) in June, Apple announced a requirement to be enforced by the end of 2016 — apps submitted to the App Store must support ATS. Just before Christmas, however, Apple postponed the deadline. Right now, it’s not clear how long Apple plans to suspend the requirement. But don’t delay. Take action now to support ATS in your iOS apps.
How many iOS apps currently support ATS?
An updated analysis of 201 of the most downloaded free iOS apps on the App Store shows that 80 percent do not support ATS (again, indicated by a NSAllowsArbitraryLoads key set to True). While it’s a limited sample, it suggests that iOS developers are not heeding Apple’s call.
Is there any good reason to disable ATS?
Unencrypted communications between an iOS app and back-end servers exposes sensitive data. Unprotected app data violates your users’ privacy and increases the risk of a security incident. A failure to protect users can damage your brand, inhibit user adoption, increase churn, and threaten revenue streams.
Developers can ask Apple for exceptions to the rule with justification. MoPub, a mobile ad-hosting provider owned by Twitter, states that one possible justification is “loading web content from a variety of sources (for ads).”
Enabling ATS isn’t necessarily easy. Depending on the number of domains or third party libraries an app needs to function, configuring the servers to communicate with a mobile app over HTTPS can add up to a lot of effort.
That’s why the time is NOW to begin enabling ATS globally across your portfolio of iOS apps. CISOs, developers, product owners, and security professionals that haven’t already implemented ATS need to plan for and kick-off their transition. Enabling ATS protects your organization and customers and prevents a last minute scramble when Apple sets a new ATS enforcement deadline.
How to implement ATS support
You will need to work with multiple teams in your organization to implement ATS globally. So start the conversation now. At the least, you will need to involve the network, web, product management, and security teams (and potentially your service providers).
You can start by inventorying back-end calls made by your iOS apps (mobile app security testing can help find them), so that you can achieve the following:
- Identify each service the app relies on
- Understand where those services are located
- Determine the people responsible for the hosts (you will need to work with them to configure the servers appropriately)
You can find more technical details about enabling ATS in the “Implement App Transport Security (ATS)” entry from our Secure Mobile Development Best Practices. You can also reference Apple documentation on the subject in their developer guides and sample code.
Conclusion
Despite Apple’s indefinite delay of the ATS enforcement deadline, do not wait. You owe it to your organization and customers to secure sensitive data transmitted between your iOS apps and back-end services. You may have a lot of work ahead of you and should get started to avoid a stressful, panicked rush when Apple issues a new deadline (which for the sake of mobile security, they ought to do).





