Defense in Depth: A Layered Approach to Mobile Security with MDM, MAM & Mobile App Vetting
Posted by NowSecure Marketing
You can’t slay the mobile app threat monster with any single silver bullet. However, identifying and mitigating risks across the broad mobile attack surface is possible – and necessary! It requires a layered, defense-in-depth approach and an acknowledgement that no silvery solution exists to cover the entire mobile security spectrum. To minimize risk, mobile security requires a balanced mixture of multiple countermeasures and technology.
The best approach to minimizing mobile app risk and data leakage is comprehensive mobile app security testing to identify security, privacy, and compliance vulnerabilities using static, dynamic, and behavioral analysis — and then fixing those flaws. However, when it comes to Apple® App Store® and Google Play™ store apps, enterprises do not have direct control over 3rd-party app developers or those developers’ internal appsec testing programs. In those cases, mobility and security teams need a reliable source for deep security testing information about those 3rd-party apps (and any updates) in order to make the lowest risk certification and whitelist/blacklist decisions.
Enterprise mobility management (EMM) and mobile device management (MDM), containerization, mobile app security testing and certification, and 3rd-party mobile app vetting or mobile app reputation services (MARS) all play an important role in a solid, effective mobile app security strategy. A combination of multiple mobile app security layers ensures that security is a sum greater than the total of its parts.
Mobile security vs. traditional security
Learning lessons from the PC-era, mobile OS vendors have built mobile operating systems inherently more secure than the traditional desktop. However, a fragmented mix of mobile apps from diverse sources, continuous network connectivity, and multiple embedded sensors transform mobile devices into potential corporate espionage devices. The volume and speed of mobile apps released each day means the quality and security of those apps varies widely. Bring-your-own-device (BYOD) and bring-your-own-app (BYOA) trends also erode the traditional security perimeter, obscure visibility into mobile devices pregnant with potential risk, and erase any semblance of control over the devices.
Let’s take a quick look at the mobile attack surface, why no one technology solves the mobile security problem, and the questions to ask yourself as you develop your mobile security defense-in-depth strategy.
Mobile Attack Surface: Four Dimensions
Overall, the mobile attack surface comprises four potential vulnerability points: the device itself, the apps installed on the device, the networks to which the device connects, and backend services used by the app.
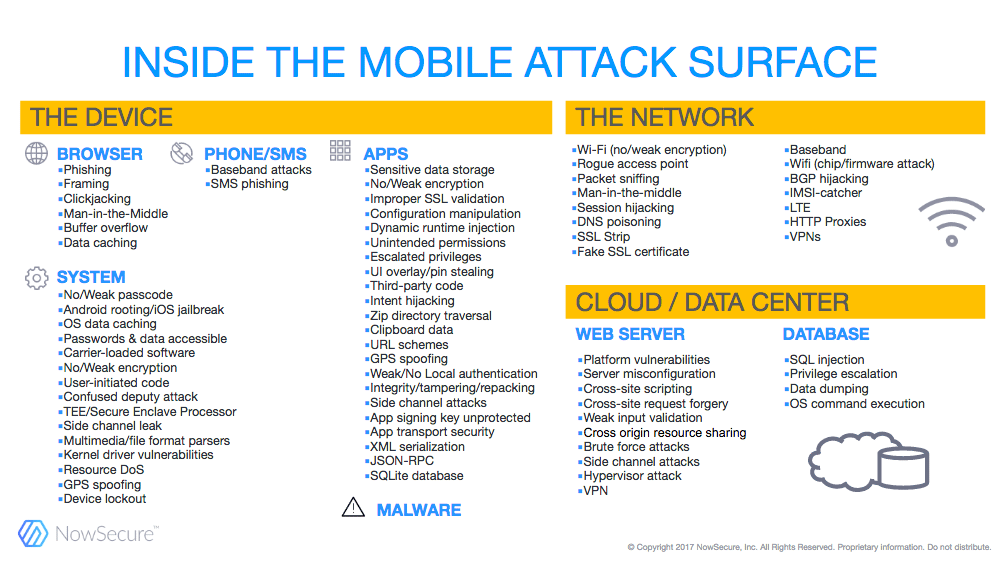
Various mobile security solutions on the market can protect data on the device, app data, or data sent over the network — but not all three simultaneously or with sufficient quality and efficiency. And no single solution covers off on all four dimensions of the mobile attack surface.
Enterprise Mobility Management
Enterprise mobility management (EMM) solutions combine Mobile Device Management (MDM), Mobile App Management (MAM) and, optionally, container and wrapping technology.
Mobile Device Management (MDM)
To start, MDM focuses on managing and configuring mobile devices within the enterprise — they are not security technologies in and of themselves. Of course MDM’s ability to enforce policy supports an enterprise’s security strategy, but MDM does nothing to directly protect internally developed or 3rd-party app data on the device.
MDM functionality can differ from vendor to vendor, but important features include:
- Pushing secure configuration profiles to Android and iOS devices
- Identifying and quarantining compromised, out-of-date, non-compliant, or compromised devices
- Enforcing PIN/Passcodes on employee devices
- Facilitating remote wiping of lost or stolen devices
- Enforcing app whitelist/blacklist
Some employees think MDM software is too intrusive for their personal devices, so achieving adoption can be challenging in BYOD scenarios. However, for corporate-managed devices, MDM provides great efficiencies in configuring and deploying more secure mobile devices.
EMM technology with MDM can help enterprises go mobile more securely as part of a layered strategy. But MDM alone does not secure the mobile enterprise.
Mobile App Management (MAM)
As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices and provides an internal company app store for employees to choose and download apps as well. While MAM technology can enforce app whitelist/blacklist, it does not include any mobile app security intelligence to help IT/security teams identify risky apps or apps that are or are not safe for corporate use.
Some vendors have extended MAM technology to append security functionality to mobile apps. This is typically done by either injecting an SDK into an app’s code (i.e., mobile app containerization) or “wrapping” the app binary to add new dynamic libraries (i.e, mobile app wrapping). Containerization and wrapping do not address the underlying problem of improperly coded apps that have security, privacy, and compliance vulnerabilities within the app itself — it’s a bandage rather than a cure, especially when it comes to 3rd-party apps. Even if it were possible to reliably containerize every app (which is not), the approach still breaks down because most if not all 3rd-party app vendors refuse to build multiple versions of their products for multiple containers. And even if an app is containerized, it still doesn’t guarantee that the app is free from all security, compliance, and privacy vulnerabilities. The mobile app still needs to undergo mobile app security testing to know for sure.
The best way to ensure the apps your organization uses are secure is to subject them to mobile app security testing. That way you have empirical evidence of an app’s security status. Though some enterprises do still find value in leveraging mobile app containerization and mobile app wrapping technologies for key organization apps as part of a layered security approach.
Mobile App Containerization
Mobile app containerization isolates a group of mobile apps on the mobile device itself in a protected layer of code and runtime services. Mobile app containerization, however, requires that app developers include an SDK in their code in order to integrate with the container solution. Mobile app container vendors typically ship core containerized apps for e-mail, calendar, contacts, notes, documents, and messaging. Some vendors have partnered with certain 3rd-party app vendors to integrate into their container as well via an SDK. Mobile app containers typically protect from data leakage, enforce secure VPN connectivity, block cut/copy/paste functionality and prevent file storage outside of the app. Mobile app containerization can provide an additional security layer for apps that the enterprise manages — whether developed internally or by selected 3rd parties.
Mobile App Wrapping
Mobile app wrapping takes another approach to securing mobile apps by protecting apps individually and not requiring an app developer to integrate an SDK. Instead, the mobile app binary is “wrapped” — typically by decompiling, injecting code, and re-compiling with additional dynamic libraries — to alter certain calls made by the target app. Mobile app wrapping provides various protections such as blocking cut/copy/paste functionality within a sensitive enterprise app among others.
Limited Mobile App Vendor Support for Containerization & Wrapping
Mobile containers and app wrapping have fundamental limitations. The main challenge with a container strategy is not all 3rd-party mobile apps required by employees for organization use can, or will, integrate into the container provided by 3rd-party vendors. In addition, not all 3rd-party apps are “wrappable” due to various coding libraries and app functionality.
Many of the top organization apps in the office productivity, customer relationship management (CRM), enterprise resource planning (ERP), financial management, health care and other genres don’t offer containerized versions and fail when a wrapper is applied to them. So enterprises are left to deploy non-containerized versions of those apps and accept the associated increase in risk, or, refuse to deploy the apps to minimize risk but then frustrate employees and inhibit organization productivity.
However, by adding 3rd-party mobile app vetting for standard non-containerized apps, an organization can test all apps to ensure they meet corporate security, privacy, and compliance policies and then reliably deploy them to get maximum organization benefit. And in the end, it’s better to have visibility into the security status of those apps rather than be left in the dark.
Managing 3rd-Party Mobile App Risk
Many organizations that deploy EMM as part of their mobile security strategy recognize that 3rd-party apps support organization objectives, but there’s also a lack of security visibility into those 3rd-party apps. That’s why many enterprises approach NowSecure for a 3rd-party app vetting solution. While those organizations may use containerization and/or wrapping for a set of core mobile apps, they’re still concerned about security risks stemming from 3rd-party organization intelligence, office productivity, ERP, CRM, travel/expense-management, and other apps.
The MAM aspect of enterprises’ EMM technology enables them to inventory the 3rd-party mobile apps already deployed on mobile devices, but it fails to provide detail about the security of any unmanaged apps (such as those on public app stores). Enterprises need deeper insight into the security of those 3rd-party apps (and subsequent updates). In the end, they chose NowSecure Platform
for cloud-based mobile app vetting and mobile app reputation services (MARS) for faster, more informed decisions about certifying, whitelisting, and blacklisting Apple App Store and Google Play store apps.
Many organizations struggle to stay on top of employee requests to use 3rd-party apps for work. More than 1,400 iOS and 5,600 Android apps and updates are published to official app stores each day. No IT, security, or mobility team can realistically keep up without help. The only solution is a continuous, automated approach to testing the security and risk of those apps. And not all security intelligence about such 3rd-party apps is created equal.
NowSecure Platform has security tested millions of the most popular Apple App Store and Google Play store apps and continuously monitors both stores for new releases. NowSecure Platform performs automated static, dynamic and behavioral analysis of iOS and Android apps from the attacker’s point-of-view on real iOS and Android devices. In addition, NowSecure Platform offers MARS capabilities by monitoring 3rd-party mobile apps across versions over time.
Along with robust, detailed findings, NowSecure Platform assigns each tested app a single NowSecure Security Score (NSS) based on the Common Vulnerability Scoring System (CVSS). The single score, with the ability to drill-down if needed, gives security and mobility teams the actionable insight they need to make better, faster whitelist/blacklist and certification decisions.
NowSecure Platform customers find that the solution’s hyper-accuracy and depth and breadth of testing sets it apart from other alternatives on the market. With such deep, accurate insight, it’s the best solution to make their EMM solutions smarter and more effective.
Recommendations for a layered approach to mobile app security
There’s no one single solution that will solve the entire mobile security problem in general or mobile app security challenges in particular. While EMM solutions have penetrated the market and offer great mobile device security capabilities, they leave something to be desired when it comes to mobile app security. Mobile app management solutions such as mobile app containerization and mobile app wrapping can help, but also have their limitations.
In the end, the best approach combines the following:
- Deploying EMM with MDM to enforce policy on devices and MAM to inventory mobile apps in use
- Subjecting internally developed/managed apps to full mobile app testing for security, compliance and privacy
- Where necessary, deploying mobile app containerization and/or wrapping for core, managed apps
- Using a trusted, accurate mobile app vetting or MARS solution so you can make swift, smart decisions about 3rd-party app risk.
Experience the power of NowSecure Platform yourself and see how it can augment your mobile app security strategy — request a free security report for an Apple App Store or Google Play store app of your choice today.





