Accurate, actionable mobile app security testing results: A sample NowSecure report
Posted by Keith Mokris NowSecure Marketing
With the NowSecure automated mobile app security testing solution, security professionals have the unprecedented ability to automate static and dynamic analysis for Android and iOS apps on real devices. By installing and running the apps on physical Android and iOS devices in the cloud, rather than emulators, our reports include more accurate results based on real-world scenarios. With those results, developers don’t waste time chasing down false positives and with remediation guidance included with every finding, know exactly what flaws to fix and how.
Our solution empowers users with clear results that map to industry standard app vulnerability and weakness classifications. We consider ourselves part of a bigger movement to impact the state of mobile security worldwide. So, our results link to standards like CVSS, OWASP, NIAP, and CWE.
NowSecure Lab Automated delivers results in minutes, faster than any other mobile app testing product or service available today — the report offers guidance on how mobile developers can then fix those flaws quickly and easily.
Below is a walk-through of a sample report from NowSecure’s Lab Automated solution explaining the display of results and how developers and security practitioners can use them to build secure mobile apps.
App information
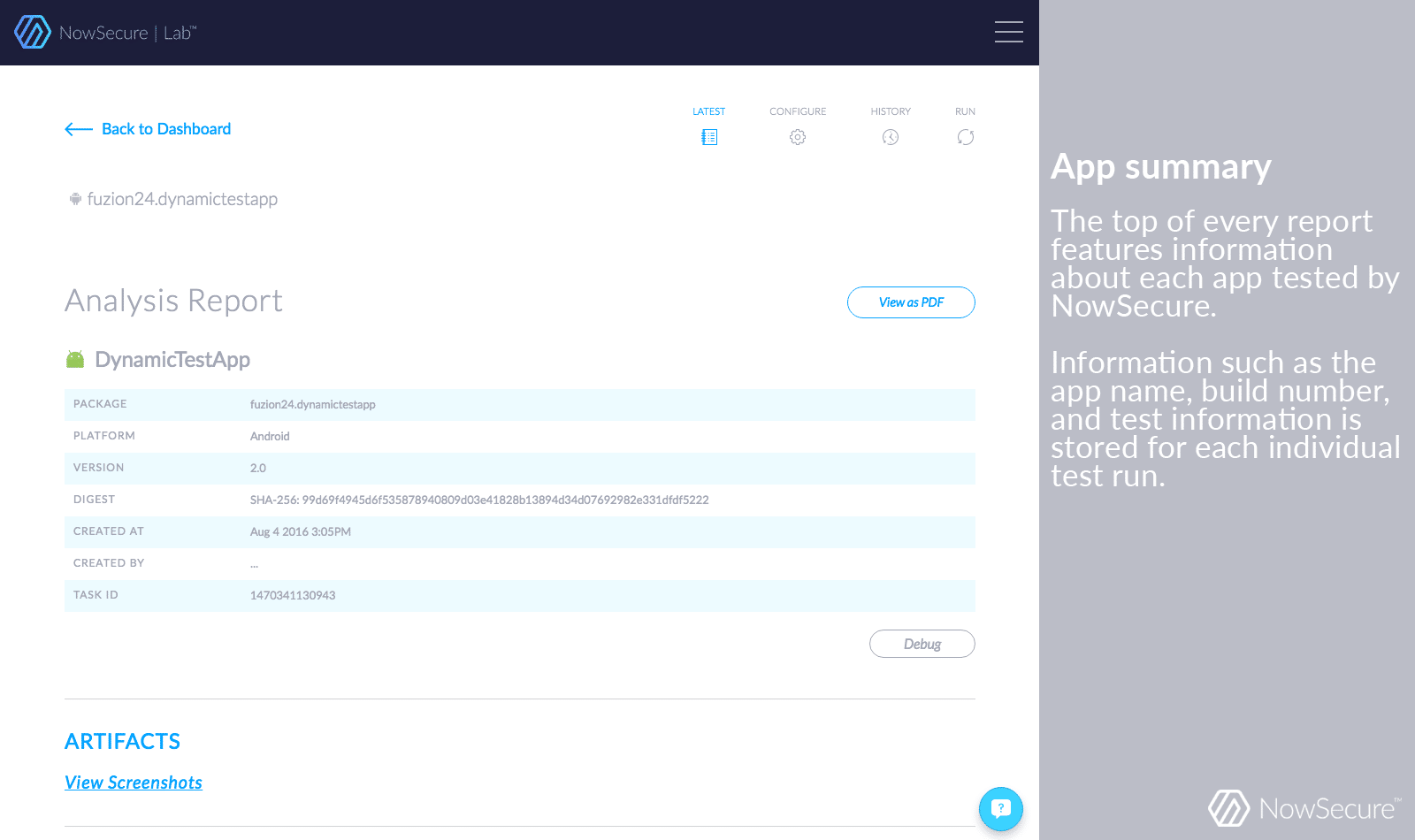
Every time you upload a mobile app, you can view a summary that records app information such as the app name, build number, and test ID — so you can track each individual test.
Live screenshots of your tests being performed on real devices
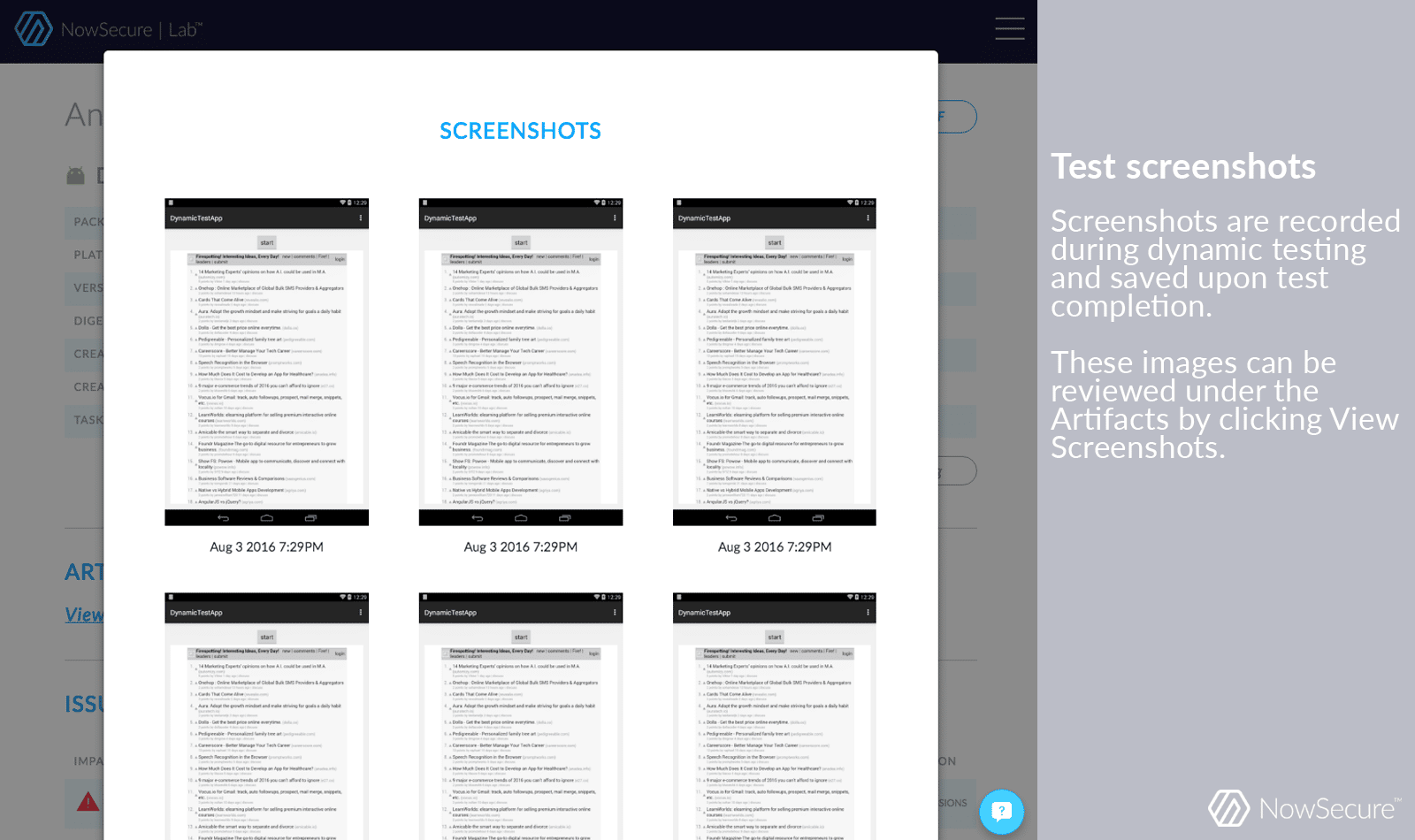
As our system performs dynamic analysis on your mobile app, users can watch live as the tests execute and keep track of the assessment’s progress.
Issues summary
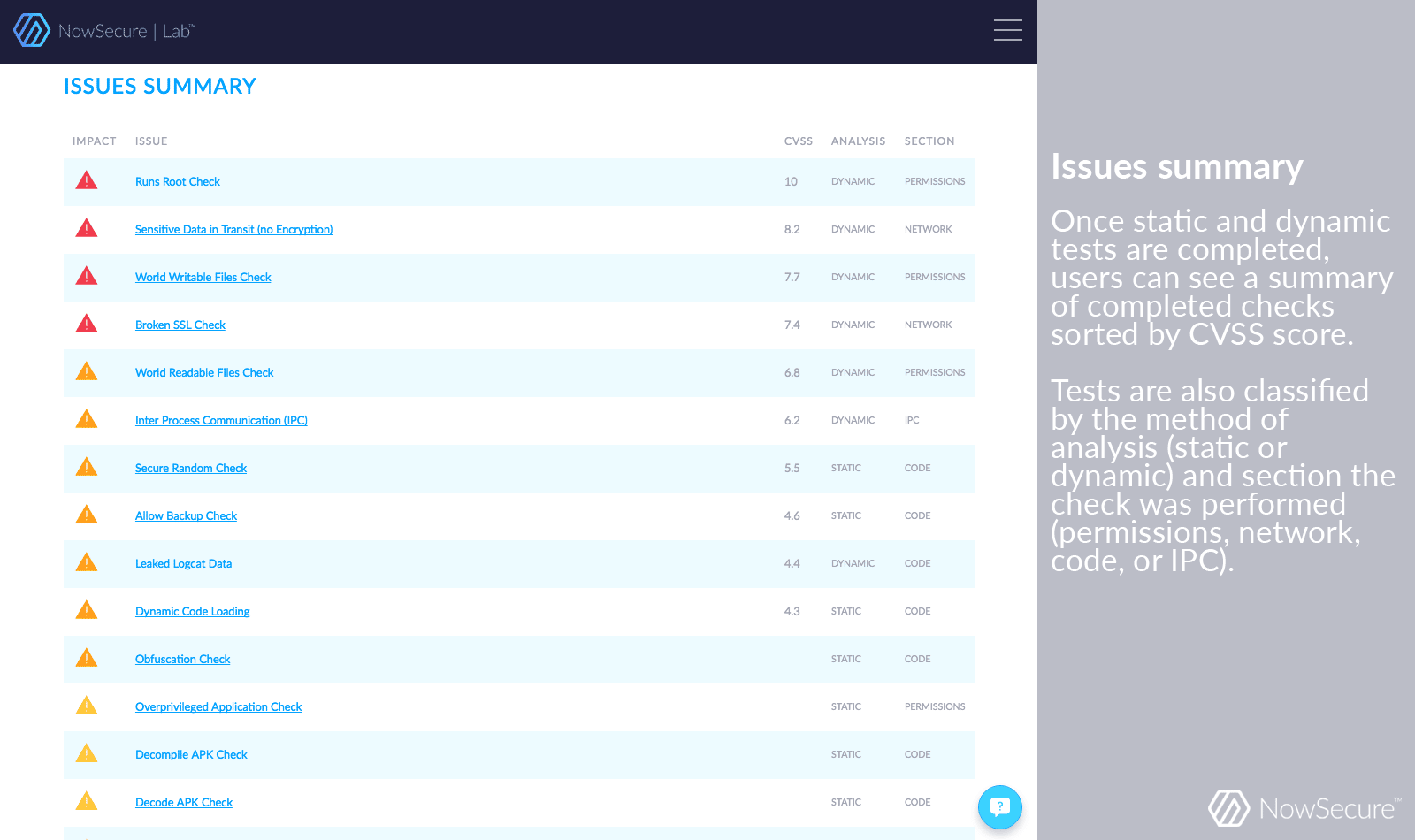
Once static and dynamic analysis completes, users can review the “Issues Summary.” The summary sorts issues by the Common Vulnerability Scoring System (CVSS), the universal open and standardized method for rating IT vulnerabilities and determining the urgency of response.
The summary includes whether the issue was identified as part of static or dynamic analysis and whether the flaw falls within the apps’ permissions, network connections, source code, or other categories.
Example issue featuring CVSS score, CWE data, and OWASP info: Broken SSL check
Clicking on any one of the issues in the summary will provide more detail.
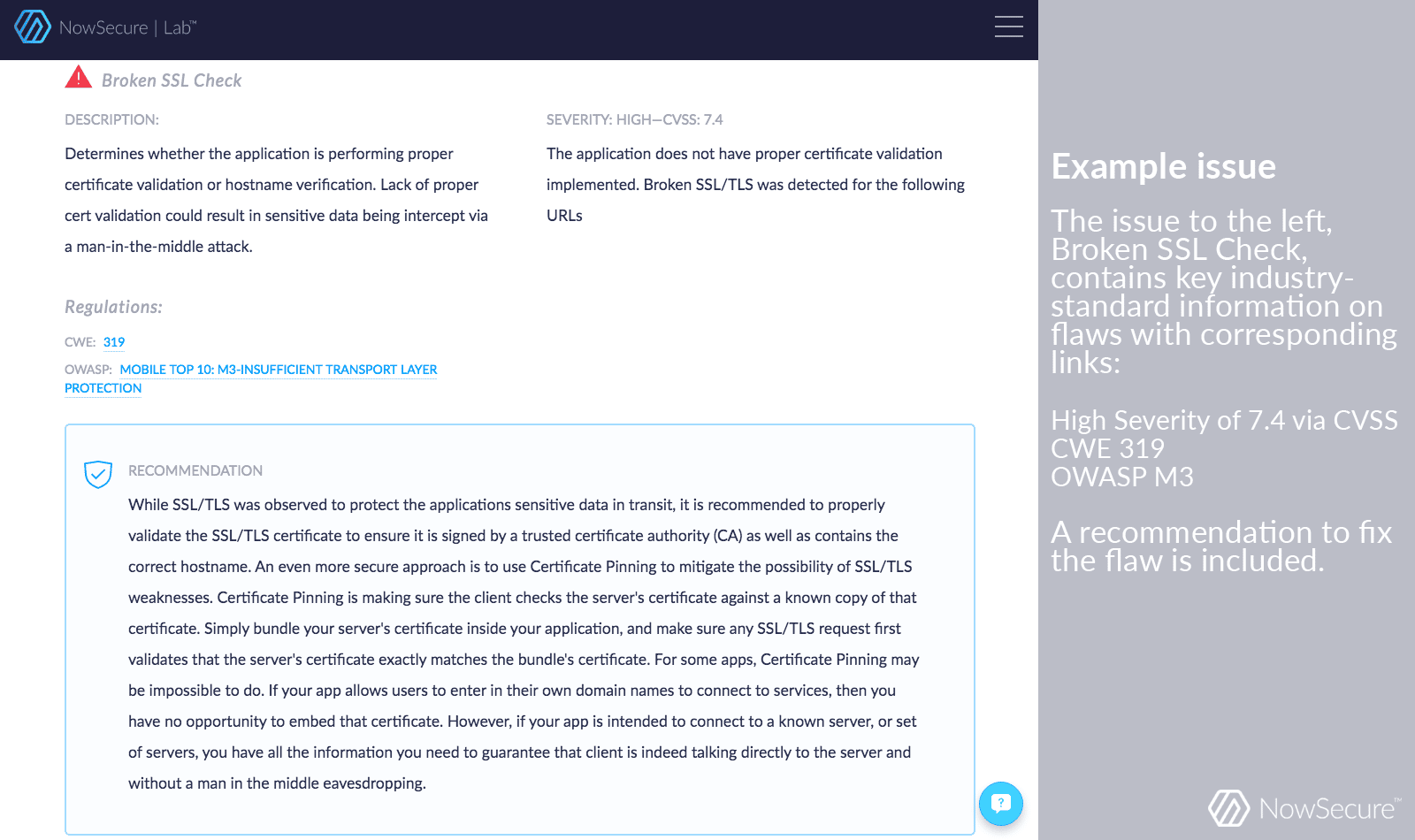
The example “Broken SSL Check” issue includes a description, severity score, a list of relevant industry standards (“regulations, and a recommendation for how to address the flaw. This check determines whether the app is performing proper certificate validation or hostname verification. Lack of proper certificate validation could result in sensitive data being intercepted via a man-in-the-middle attack.
Our reports rank severity based on CVSS scores. In this example, the app tested was vulnerable to this flaw with a CVSS score of 7.4, making it a high risk flaw. Users can also see relevant Common Weakness Enumeration and Open Web Application Security Project (OWASP) Mobile Top 10 information.