Top Mobile App Vulnerabilities: How to Protect Your Business from Hidden Security Risks
Posted by Amy Schurr
What risks lurk in your mobile app ecosystem? Mobile apps play a vital role in customer engagement and business operations, but they also bring unique security and privacy risks. Unlike traditional desktop applications, mobile apps run on diverse devices and operating systems, increasing their exposure to vulnerabilities.
Mobile app risks can range from insecure data storage and weak authentication to vulnerabilities in third-party libraries or APIs. These flaws may lead to data breaches, unauthorized access or regulatory fines and penalties, posing serious threats to both users and organizations.
Mobile app risks can range from insecure data storage and weak authentication to vulnerabilities in third-party libraries or APIs.
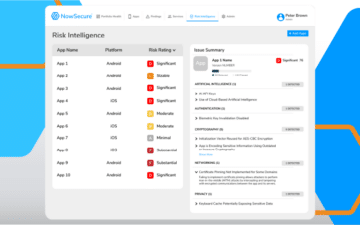
Our latest infographic highlights five common mobile app security and privacy risks uncovered by NowSecure Mobile App Risk Intelligence (MARI). Such insight will help security and end user computing teams proactively manage risks throughout their mobile app ecosystems by determining which apps are safe for employees to use.